This article is more than 1 year old
Naked at 30: Osborne 1 stripped to its chips
He ain't heavy. He's my TV typewriter
Mega-floppies with mini-capacity
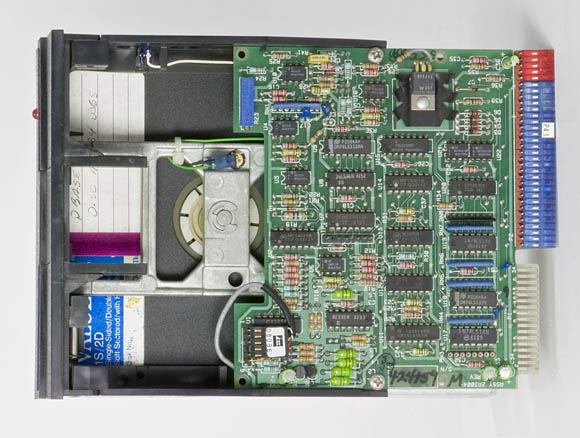
If you've been around personal computers for a few decades, you'll remember when floppy disks were, well, floppy. The dual 5.25-inch drives in the Osborne 1 used those flexible, black-sleeved disks, the decendants of earlier 8-inch floppies.
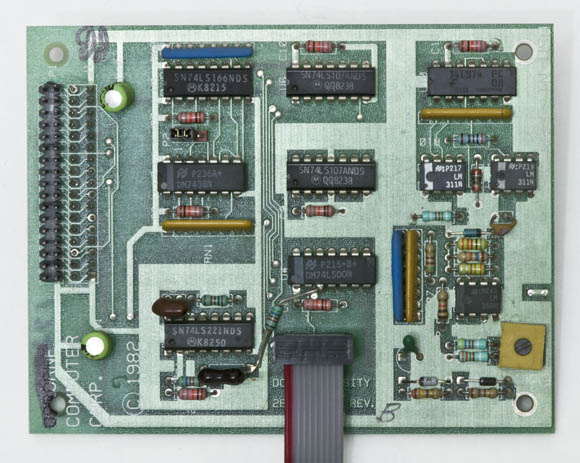
The original machine accepted only single-density disks with the amazingly miniscule capacity of 92KB. A double-density, factory-installable optional card, however could just about double that capacity, bringing it up to 182KB.
According to Oldcomputers.net, the double-density option allowed the floppy drives to also read disks formatted as Xerox 820 single density (82KB), Cromemco single density (80KB), IBM Personal Computer (156KB in the CP/M-86 format), and DEC VT-180 (171KB).
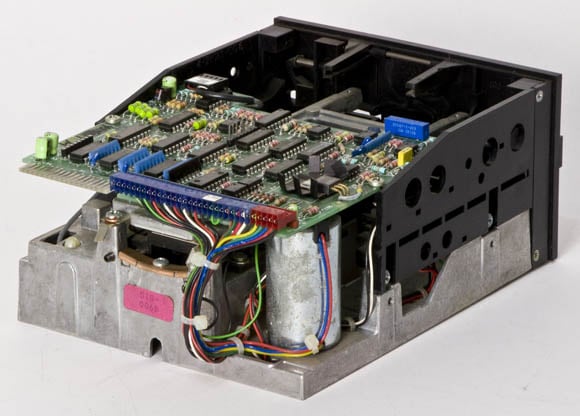
Here are a few views of the full-height 5.25-inch drives in the Osborne 1:
As large as these floppy drives now appear, they were compact when compared to the 8-inch drives in my teardown of an S-100 system that I built oh, so many years ago.