This article is more than 1 year old
Samsung BD-D6900 3D Blu-ray player and DVR combo
Does it all and then some
Flash plug-in support?
The system functions as a DVR when partnered with a USB hard drive. Initially I attempted to make recordings onto USB flash drives, however these failed the deck’s format and testing routine. I eventually settled on a 250GB Seagate Freeagent Go external drive, which worked fine.

TV Guide
You can access the drive from the My Recordings tab and here you’ll find neat animated thumbnails of your programmes. Recordings replay without snitches or glitches – but you cannot Chase Playback. Once you’ve initiated a recording, you have to kick your heels until it’s done before you can watch. All dubs are protected by steel-plated DRM.
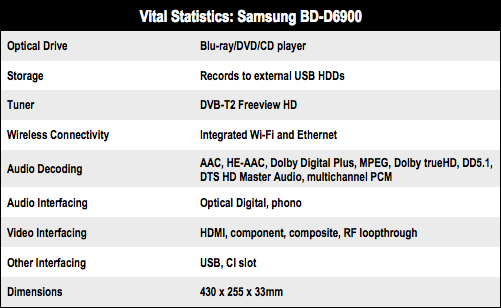
Similarly, you can’t record from the BD-D6900’s Freeview HD tuner and browse the on-line Smart Hub portal at the same time, although you can record and play a Blu-ray/DVD/CD. And with only one tuner, you cannot record one channel and watch another, you’d need to utilise the telly’s tuner to do that. Network media streaming is more like a dribble.
Despite sniffing other DLNA devices out across my LAN and identifying other DLNA devices, file compatibility proved a little patchy. There was no video support for MKV or MOVs and AVIs played albeit without SRT subtitles. MP3 rips from my Imerge Musicm8 server came sans artist data or album art. You may well have more luck though.

Network devices
Samsung products are a little bit picky when it comes to befriending DLNA servers over a LAN. They tend to be more co-operative when pulling content from a PC. When fed directly from a USB drive, things improve. My MKV wrappers unspooled and AVIs played back with subtitles intact.