Raising the alarm
The Zomm first appeared in the US in early 2010 but is now being officially distributed in the UK, currently in a choice of white or pink. A few similar devices have also emerged, such as the Nio, while the upcoming PipSqueak adapts the concept by adding caller ID display and call-holding.

Doubles as a Bluetooth speakerphone or panic alarm
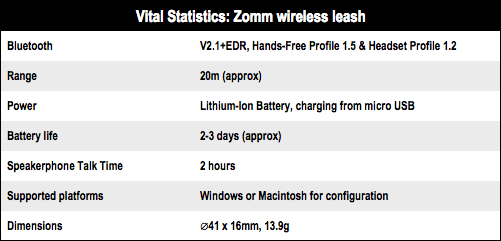
For now, the Zomm is a simple phone accessory. It takes about four hours to charge through its mains adapter or while connected to your computer via micro USB, where you also configure your preferences. Battery life lasts for about two to three days on average, depending on speakerphone usage or the number of times the alarm sounds.
The set-up is straightforward – you pair it to the phone like any Bluetooth product, and there’s only one button on the Zomm itself. The button is slightly recessed to limit accidental presses in a pocket or bag, but it’s relatively big so these could still happen. It serves as the on/off switch or, when on, to accept calls over speakerphone. Two quick presses diverts to voicemail.
When your mobile switches off – or if the battery dies – without first turning off the ZOMM then its alarm will sound. Therefore you have to adopt a new mindset to keep aware of this, especially if you’ve gone somewhere like the theatre. And although it works with most mobiles, there are quirks. With a Nokia I found the alert sounded when answering incoming calls on the handset rather than with the Zomm’s speakerphone. However, with an LG phone it worked properly.