This article is more than 1 year old
Apple Mac OS X: A decade of Ten
How about them Apples?
Mac OS X is - formally - ten years old today.
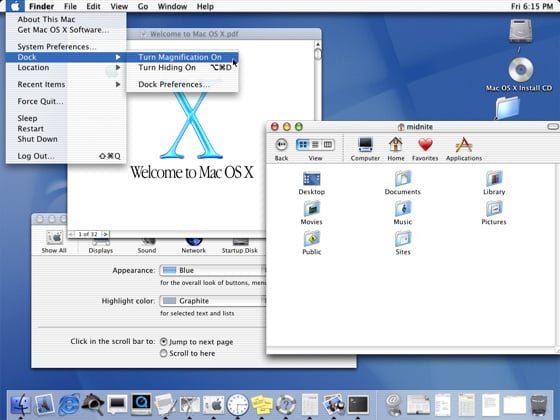
The first full release, then simply codenamed 'Cheetah' - only later did the cat branding become part of Apple's marketing drive - was made available to Mac users on 24 March 2001, six months after the operating system made an appearance in public beta test form.
OS X was the product of Apple's 1996 purchase of NeXT, a move that not only saw the acquisition of a modern operating system, but also the return of its co-founder, Steve Jobs, to the company.
Then CEO Gil Amelio saw Jobs as a key advisor in the years ahead, but soon he was out, replaced by Jobs as Interim CEO, a role maintain for a few years before becoming a more permanent appointment.
During this time, the incoming NeXT team, under Avi Tevanian, worked to re-skin NeXT's OpenStep OS with a Mac OS-style user interface that would become branded Aqua. The initial version of OS X was codenamed 'Rhapsody'.
OpenStep's foundation was entirely different from the existing Mac OS. It was written for Intel CPUs, for instance, leading some pundits to forecast a move from the Mac's PowerPC platform to the x86 architecture. It did happen, but not until 2005 - and not until it was evident to all that the PowerPC line had run its course as a platform for desktop and, in particular, laptop computers.
No cat branding on this carton
But in a bid to provide backwards compatibility, Apple's software engineers created a Mac OS 9 - from then on dubbed the "Classic Mac OS", virtual machine to run inside Mac OS X. When double-clicked - from the new "Applications (Mac OS 9)" folder - old apps would load themselves into the VM and run.