This article is more than 1 year old
Nokia Software Updater for Mac Beta
Beta late than never?
Not so suite
I still use an N97 Mini because navigation with Nokia’s off-line maps is just so darned handy when travelling abroad, as you don't have to worry about data charges. Having taken this Nokia on holiday recently, I’d actually fully updated the phone from within my Parallels Win XP virtual machine, but I was still curious to find out how the Nokia Software Updater would perform. First things first though, you need to be registered with Nokia to get the update. If you’ve an Ovi login, then this will suffice.
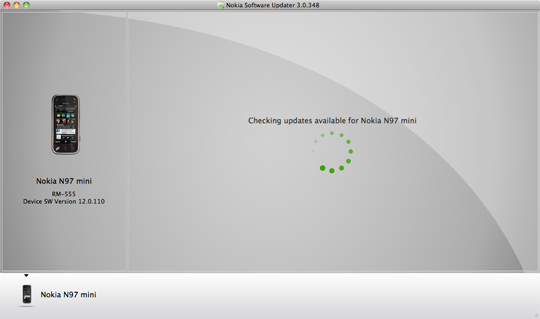
Detecting
The application download weighs in at 12.4MB, instals in seconds and takes up 34.7MB of disk space. Running it checks for a connected phone, which we’re warned should have a direct USB connection – no hubs or tacking on the end of a keyboard. With the device detected – I didn’t even need to select PC Suite on the phone for it to be recognised – the Nokia Software Updater then does what it says on the tin and sets about checking for updates.
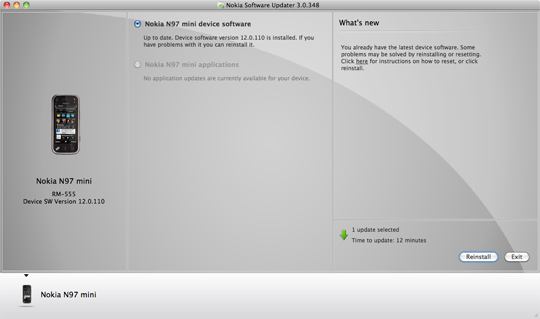
As expected, the application reported my N97 Mini was up to date. The phone applications update section was greyed out, as this feature is unsupported by this beta. However, there is an option to reinstal the current system software. The ‘What’s New’ section features a link that brings up documentation advising on resets and the like. Below is the Reinstal button with an update estimate suggesting it should take a mere 12 minutes.
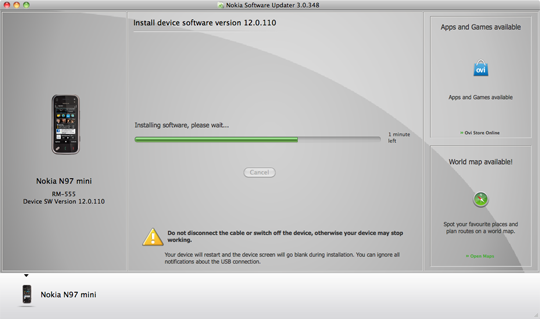
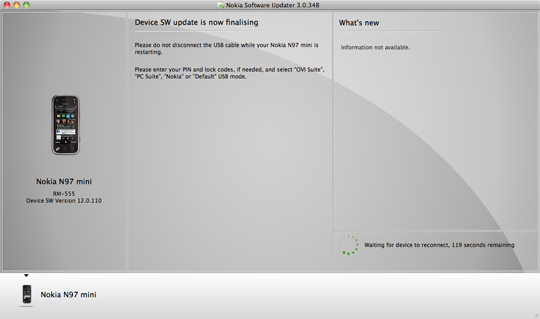
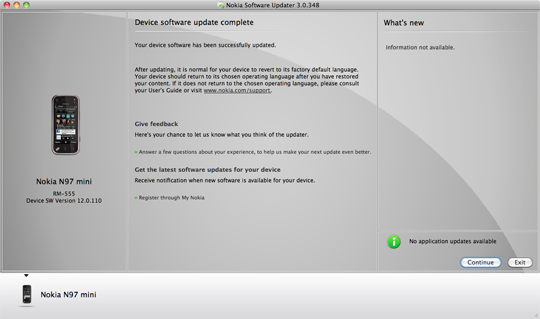
Your mileage may vary, as the updater pulled in over 165MB of system update for the N97 mini before commencing the reinstallation. Offering the online equivalent of elevator music, the installer shows links to the Ovi site and Nokia Maps, which didn’t load initially, but a browser refresh woke things up. Twenty minutes later, all was good and following this process there had been no change in the memory/storage usage either.