This article is more than 1 year old
WTF is... cloud gaming?
Look, ma, no console!
Play at home, play on the move
Gamers can also continue from where they left off - on different devices. Sony clearly shares the view that this is a benefit and recently launched a cloud-based save-game option for PS3 owners. It's easy to imagine this service extended to allow mobile play of the same title on Sony's upcoming NGP handheld - and maybe Android smartphones too.
Some big names are signing up
OnLive has its eye on phones. Last month, it announced a deal with HTC that will see the phone maker embed OnLive software in its smartphones. There is already an app for iPad. This currently only offers a view mode, a window to watch other gamers at play, but it may not be long before users can fully access OnLive from their tablets.
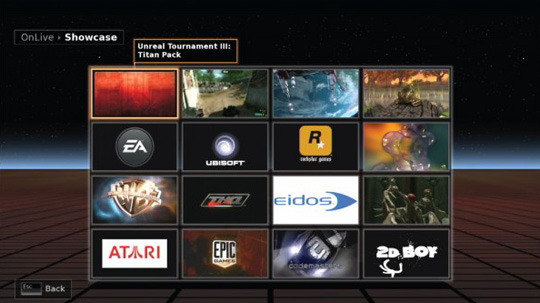
OnLive was in development for eight years before it launched in the US in June 2010 and the company has spent a lot of that time working to cement relationships with game studios. More than 20 publishers have now contributed to the service, and over 40 titles are available. But not all developers think the service can survive.
Cevat Yeril, CEO of Crysis creator Crytek, reckons repackaging titles already available on other platforms is not the way to build a successful business model. While recognising the service as the "great first-mover" of cloud gaming, Yeril believes OnLive is unsustainable in the current market. It lacks, he says, a "killer app", an exclusive title which clearly demonstrates that the service's capabilities are superior to those of other platforms.
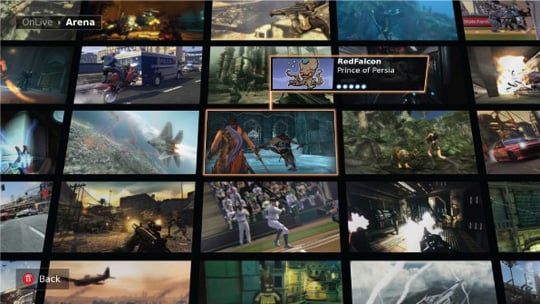
Watch other people play
However, the key issue that faces OnLive - and its rivals - centres on streaming such high volumes of data. To present a game in 1280 x 720 resolution (720p), OnLive says a consistent 5Mb/s stream is needed. An hour's play will consume just under 2.3GB an hour, at that rate. Here in the UK, data caps are commonplace, and many ISPs throttle traffic if they consider too much data is being transferred.
