This article is more than 1 year old
Apple MacBook Pro 13in
Shiny, silver Sandy Bridge system
Case hardened
Since Thunderbolt connectivity is provided by the MBP's DisplayPort mini connector, the only difference between the 2011 model's port array and that of its predecessor is the tiny Thunderbolt logo. Otherwise the two machines look exactly the same.
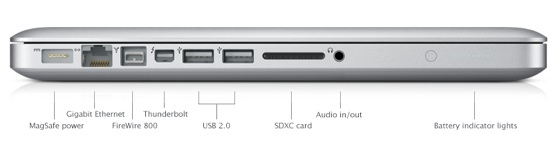
Port array almost unchanged: now with Thunderbolt
And, yes, the 13in MBP still has a combined 3.5mm audio I/O jack, so you can't use headphones and a microphone at the same time, unless it's in the dongle on a pair of phone-oriented 'phones. Their controls will work too, though the Mac disconcertingly cuts the audio off if you sit listening to nothing for too long - presumably a power-conservation trick.
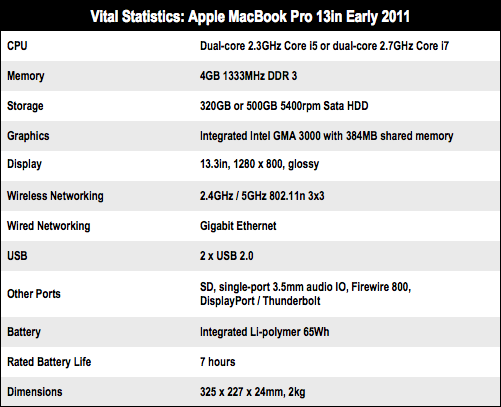
Just like the port array, the rest of the machine's casing remains unchanged. The changes here are internal: upping the processor from a two-core, two-thread 2.4GHz or 2.866GHz Core 2 Duo to the 2.3GHz Core i5-2410M or the 2.7GHz i7-2620M, skipping the generation of Intel mobile CPUs between them.
The i7, which I tested, has two cores, but the presence of HyperThreading makes it look like a quad-core CPU to Mac OS X - though it won't deliver full quad-core performance. The new i5 is the same two-core, four-thread architecture, but has 3MB of top-level cache to the i7's 4MB.
Both chips feature a Turbo mode clocking the frequency of a single core up to 2.9GHz (i5) or 3.4GHz (i7) if the chip can do so without over-heating. It can overclock both cores too, but the peak speed won't be as high.