This article is more than 1 year old
Turing Collection saved for the nation
Bletchley Park to house codebreaker's papers
The Turing Collection - the set of offprints of Alan Turing's work collected by his friend Professor Max Newman - has been saved for the nation after the last minute arrival of money from the National Heritage Memorial Fund.
Earlier fundraising failed, despite help from Google and private donations, and the collection was put up for auction at the end of last year.
But bids dried up at £240,000 - less than the lot's reserve price.
The National Heritage Memorial Fund has now provided the missing funding. NHMF is paying £213,437 which will be added to £28,500 donated by the public, $100,000 from Google and a "significant sum from a private donor".
Dame Jenny Abramsky, Chair of the NHMF, said: “This is such welcome news. Alan Turing was a true war hero and played an absolutely crucial role during the Second World War... this grant will now ensure that this extremely rare collection of his work stands as a permanent memorial to the man and to all those who paid the ultimate price in service to this nation.”
Saving the collection is particularly welcome since Turing left very few physical traces. Almost all the papers at Bletchley Park were destroyed after the war and Turing kept little himself.
Turing is chiefly famous as the UK's "father of computing". His codebreaking work with colleagues at Bletchley Park, apart from shortening the war by two or more years, laid the foundations of much modern computing.
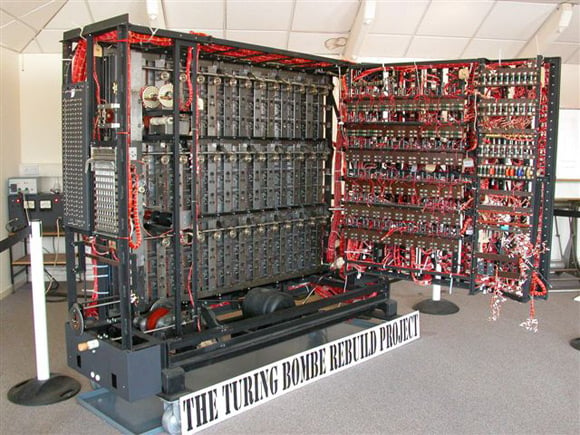
The rebuilt Turing Bombe used to decrypt Enigma-coded messages.
He was also forced to undergo chemical castration after being convicted of homosexuality in 1952. This cost him his security clearance for his then job at GCHQ.
He is generally believed to have killed himself in 1954 by eating an apple containing cyanide. His mother believed his death was an accident caused by lab chemicals.
In 2009 then prime minister Gordon Brown made a public apology for Britain's "appalling treatment" of Turing. ®
