This article is more than 1 year old
RIM BlackBerry Bold 9780 smartphone
Cosmetic treatment?
Review If you’ve seen one BlackBerry, you’ve sort of seen them all: the latest models nearly all talk the same design language of smallish screen and biggish keyboard, the unchanging row of buttons and, generally a chrome frame.
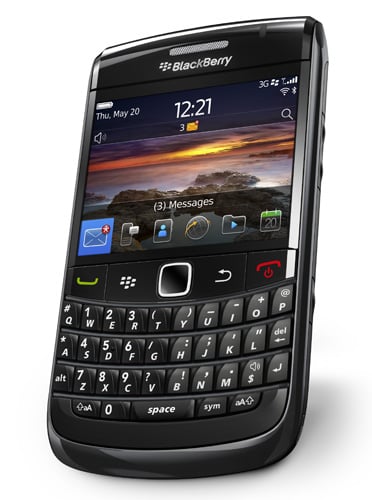
Refashioned but still unmistakable: Rim's BlackBerry Bold 9780
And despite the fact that everybody who has one uses it for e-mails, Research in Motion doesn’t see fit to put the @ and full stop characters – which are essential in every email address –on lower-case keys on its BlackBerry devices. True, if you’re entering such an address you can press the space bar and the software knows to translate, but it still slightly beggars belief. Never mind.
So what’s new on this phone, the latest in the Bold series which sits at the top of the company’s range? Well, that de rigueur chrome frame has gone, replaced by a shiny black trim. The chrome “guitar frets” that sit between the rows of keys and improve typability are now also black. The leather-like panel on the back door now has a finer grain to it.
And that’s it. Otherwise the 9780 looks identical to its earlier sibling, the 9700. No problem, since the 9700 was a splendid phone, so it’s still light but reassuringly solid. It has an exceptional keyboard, thankfully unchanged from the 9700, and an efficient, if idiosyncratic, operating system. And it’s the operating system which has improved, using the new version first introduced on the Torch.
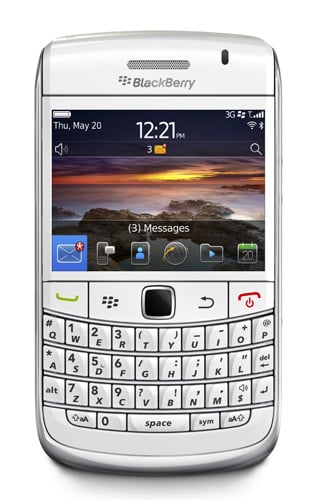
Also available in white
True, the screen, still a 2.4in model, looks a little stingy next to many touchscreens but this just reinforces the fact that this is a handset for work more than for video playback or hardcore gaming. Plus, if you want a big screen, as well as the peerless BlackBerry keyboard, you can opt for the Torch but I’d say the Bold is much more manageable than the somewhat bloated Torch.
