This article is more than 1 year old
Intel outs future Xeon chip porn
Get a load of them cores!
Twelve cores. Two amputated
There are six cores and matching L3 caches on top of the uncore, and four cores and their caches below. Yup, you got it. The Westmere-EX is actually a twelve-core design that had two cores cut off. (Intel didn't say that at ISSCC, but I am saying it and it is obviously true.) So when Intel does a process shrink to, say, 28 nanometers it will be able to tack on those two cores, crank the clocks, and put out a Xeon 7700 in fairly short order if it needs to.
Sawant said that the Westmere-EX chip had two integrated DDR3 memory controllers, which are at the bottom of the chip (labeled SMI I/O, short for Scalable Memory Interface). These controllers will support up to eight DDR3 memory channels. The chip has four QPI links along the top, and they will run at the current top-end 6.4 GT/sec speed that the Boxboro chipset supports. Intel probably won't crank QPI up to 9.6 GT/sec until another chip and chipset redesign comes down the pike. The Core C6 power states that came out with earlier "Westmere-EP" Xeon 5600 processors last year are being pulled into the Westmere-EX design.
The Westmere-EX chip will use a bi-directional ring to link all of the L3 caches to all of the cores on the chip. The routers to control this ring interconnect are to the left and right of the QPI routers at the center of the chip and have a dozen ring stops where the two rings, etched in metal layers 7 and 8 on the chip. (The Westmere-EX is implemented using Intel's nine-layer 32 nanometer wafer-baking process, which adds in strained silicon.) Here's what the rings look like, conceptually:
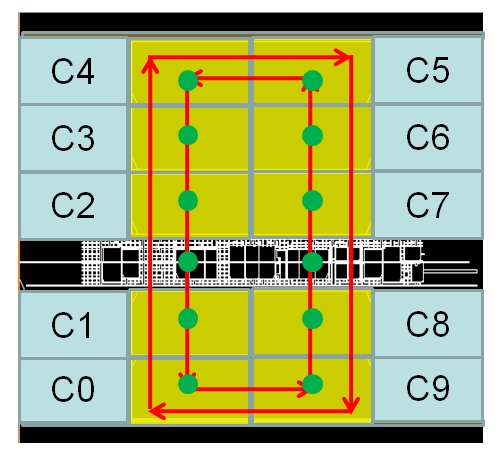
The rings use a 32-byte wide data path, which is half the width of a cache line, and more than 1,200 wires in layers 7 and 8 of the metal comprise this ring interconnect. With each tick of the CPU clocks, data can move one stop on the ring either clockwise or counter-clockwise.
Sawant says that the Westmere-EX chip has 1,567 pins, with 717 of the pins being dedicated to signal I/O. Here's what the Westmere-EX package looks like from the outside:
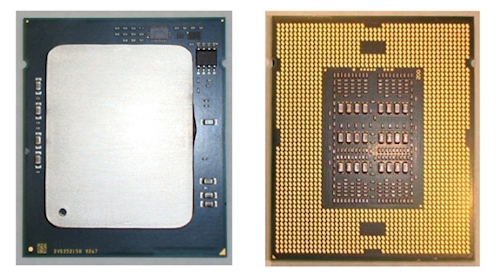
The package measures 49.1 millimeters by 56.4 millimeters and uses a 14-layer organic substrate. The heat spreader on the top of the package measures 35.5 by 43.1 millimeters.
