This article is more than 1 year old
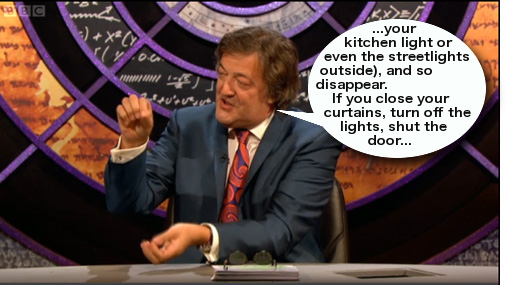
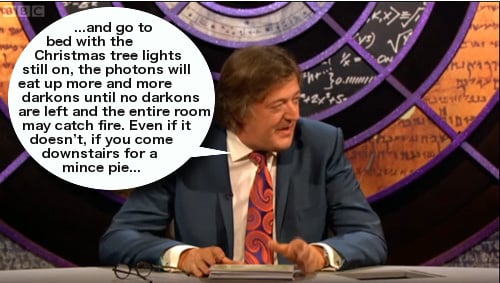
Stephen Fry explains ... How Christmas Tree Lights Work
Where you get to be a National Treasure™
Careful with that mince pie

Splendid work Simon, thank you. We would nominate you for a BAFTA and a building society commercial voiceover – if only we could.
But can you improve on this? You can pick any technical or scientific subject you like. The details of our one-click submission process are below. Plain old text is welcome - we can add the dramatic visualisations.
But remember: the explanations must be wildly inaccurate, demonstrating a fundamental misunderstanding of engineering and physics. One or two entrants erroneously submitted technically accurate descriptions of things in Fry luvvie-speak. This will not do.
Shove your entries into our postbox. ®
