This article is more than 1 year old
Mysterious crypto-book dated to 15th century
Real life Da Vinci codex features nude ladies, too
A mysterious book written in a language or code that no cryptographer has ever managed to crack has been verified as being written in the early 15th century, which has upset some of the theories on its origin.
People were making up garble-languages well before J R R Tolkien came along
The "Voynich manuscript" was found in 1912 at the Villa Mondragone, a one-time papal palace complex near Rome which was at the time being used as a scientific college by the Jesuit order of the Catholic church – formerly famous for their deviousness and secrecy. Book dealer Wilfrid Voynich found the tome among a chestful of volumes offered for sale by the Jesuits.
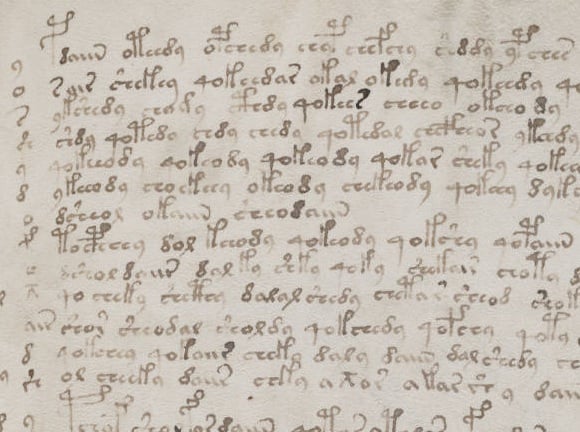
The book is full of bizarre illustrations and contains writing in an unknown and so far undecipherable script. The pictures appear to depict such things as unidentifiable plants, astronomical and astrological objects (suns, moons, stars, signs of the zodiac), curious cosmological diagrams and so forth. There is a section which mainly shows naked women in pools or bathtubs interlinked by elaborate networks of pipework, some parts of which resemble human organs.
Voynich, who died in 1930, theorised that the book had been written by the famous 13th-century friar and polymath Roger Bacon, a sort of early Leonardo da Vinci figure often credited with the introduction of gunpowder to much of Europe and conceptual invention of flying machines, steam engines etc.
This theory at least has now been conclusively disproven, as boffins at the University of Arizona have used radiocarbon dating to discover that the book was produced at some point between 1404 and 1438 – well after Bacon's time. The dating was done last year, but Arizona uni has announced the new information publicly this week to coincide with a National Geographic Channel doco.
