This article is more than 1 year old
Intel 'Sandy Bridge' mobile platform
Second-gen Core i7 CPU leaves its tyre marks
Brain drain?
The figures did throw up an anomaly though when testing battery life. Reg Hardware’s approach is to run continuous loops of PCMark Vantage until death, which typically means you can double the number to get a real world figure. The first run with the SSD lasted 91 minutes, but when I switched to the Toshiba HDD the figure increased to 106 minutes. That's an extra 15 minutes in benchmark land or roughly half an hour in the real world. And while I might expect an SSD to yield extra battery life, it came as quite a surprise to see the battery life drop.
Benchmark Tests
Battery Life Results
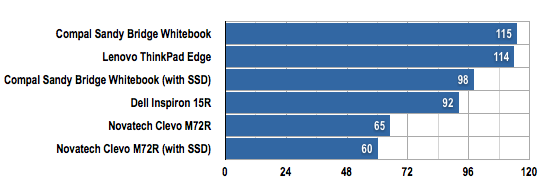
Battery life in minutes
Longer bars are better
After that I plugged in the SSD and did two more runs which came in at 100 minutes and 96 minutes so, assuming the original figure is battery conditioning, that gives an average life of 98 minutes. I then did two more runs with the Toshiba HDD and timed them at 117 and 114 so here the average is 115 minutes in favour of the HDD over the SSD.
It occurred to me that this might be a feature of SSD versus HDD rather than Sandy Bridge so I grabbed a Core 2 Duo laptop off the shelf and repeated the tests. This yielded the expected results with 60 minutes of life with the HDD and 65 minutes using SSD. Intel UK tells us they have technical people in the US looking into my findings but I have had no feedback from them in the past ten days. However, a report this week from Intel on its discovery of a Cougar Point chipset design error that impacts on Sata performance, may have a connection.
Verdict
As things stand, I am impressed by the raw power of Sandy Bridge and love the plug and play nature of Intel Wireless Display, however, there are bugs to be ironed from the My WiFi console and, so it seems, the chipset itself. ®
More Notebooks Reviews... |
|||
 Acer Acer
Asus NX90Jq |
 Apple Apple
MacBook Pro 17in |
 Samsung Samsung
R780 |
 Toshiba Toshiba
Satellite A660 |
