This article is more than 1 year old
Intel 'Sandy Bridge' mobile platform
Second-gen Core i7 CPU leaves its tyre marks
Review Sandy Bridge is the codename for Intel's second generation of Core processors that covers Core i3, i5 and i7 for both side of the desktop-mobile divide. If you've been following the news lately, you'll know that Dell has discovered flaws in the Cougar Point chipset that, while not revealing a fault in the actual Sandy Bridge CPU, has implications for Sata devices used in this new generation of silicon. In the process of reviewing this whitebook sample, issues affecting storage did come to light as, you'll discover.

Intel's Sandy Bridge 17in whitebook review sample bore a marked resemblance to Packard Bell's Easynote LM
I have dabbled with Core i5 and Core i7 Sandy Bridge desktop processors and I must confess, I’m mightily impressed by the dynamic overclocking of Turbo Boost 2.0, the power management features and the minuscule power draw. It's a strange experience watching an overclocked Core i7-2600K system running at 4.2GHz as it draws a mere 155W at the mains socket and shreds the Cinebench 11.5 benchmark into tiny pieces.
I had anticipated waiting until late February or March to get my hands on a Sandy Bridge notebook, however, Intel came knocking with an unbranded whitebook that showcases the new technology. This chimera of a laptop is made by Compal yet shows Packard Bell branding on the mouse buttons. At a guess, I’d say that the whitebook is based on the same chassis as a Packard Bell EasyNote LM.
The specification is high end and consists of a Core i7-2820QM processor, an Intel HM67 chipset, and 4GB of DDR3-1600 RAM in two modules that operate in dual channel mode. The machine came preinstalled with 64-bit Windows 7 Ultimate Edition on a second generation 160GB Intel X25-M SSD.
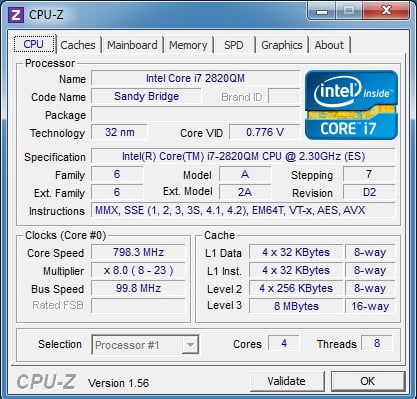
CPU-Z reveals all
On the face of it the weakest part of the specification of the unit is the Intel HD Graphics 3000 that is part of the Core i7 processor. Despite running at a sprightly 650MHz, the graphics only pack 12 shaders. At 1600 x 900 the screen resolution of this showcase laptop was a little disappointing, not quite managing Full HD .
