This article is more than 1 year old
Samsung N350 dual-core netbook
Slimmer, faster and - ahem - pricier...
Benchmark Tests
PCMark05 Results
CPU
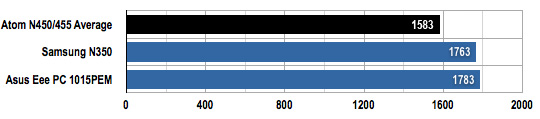
Longer bars are better
Memory
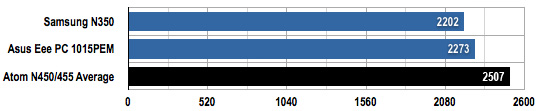
Longer bars are better
HDD
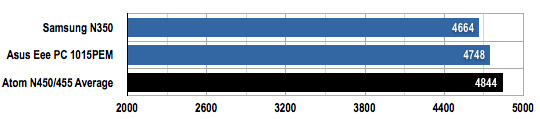
Longer bars are better
Battery Life Results
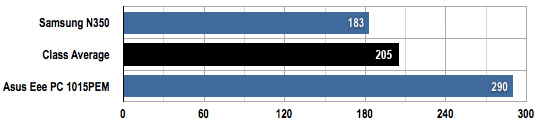
Longer bars are better
Next page:
The price is right?
