This article is more than 1 year old
Gates, Woz, and the last 2,000 years of computing
If you program it, they will come
Overcoming the odds
While you can't view the actual BASIC interpreter tape that Gates wrote, the code has been immortalized in a huge glass plaque in the newly minted, airy reception area. Nerds take note: the reception area's tiled floor holds a punch-card design – work out what it says and you win a prize.

AltaVista on the Google rack (photo: Gavin Clarke)
"Knitting it all together," as Hollar puts it, means you shouldn't be surprised to see that 1999 Google rack server in an exhibit that goes back 2,000 years to the abacus.
"Will Google be remembered 100 years from now? That's hard to say," Hollar told us. "But what's more likely is what Google represents is with us forever - which is finding what you want, when you want it, where you are, and having an expectation that that information is going to be instantaneously available to you. That's unleashed a new kind of human freedom and those powerful forces that affect people at a personal and human level – they don't get put back in the box."
Revolution doesn't just show objects that are important to computing, such as the Google rack, it also tells the stories of their creation and their creators. Not just familiar names such as Alan Turing, but also the ENIAC women whose job title was "computer" and who were classified as "sub professional" by the army and disregarded by their snotty male managers.
Also featured are people such as integrated-circuit inventor Jack Kilby, whose bosses at Texas Instruments told him in 1958 not to bother with his project. Kilby pressed on regardless during his summer holidays, and presented the top brass with the finished article when they returned from their undeserved time away. Such jaw-dropping tales of achievement against all odds are explained with the assistance of 5,000 images, 17 commissioned films, and 45 interactive screens you can poke at and scroll through.
Thanks to its location in the heart of Silicon Valley, down the road from Apple, Intel, HP, and Xerox PARC – companies whose ideas or products now dominate our daily lives – it would be easy for the museum to present only a local feel to the story of computing, and to give a US-centric bias. With displays from Britain, France, Japan, Korea, and Russia, however, Revolution looks beyond the boundaries of Silicon Valley and the US.
A good example of the global focus is the story of LEO, the Lyons Electronic Office that's one of the least-known entries from Britain in the history of personal computing.
Back when Britain ran an Empire, J Lyons & Company was a huge food and catering company famed for running a network of nationwide teashops that refreshed stiff upper lips from Piccadilly to the provinces with cups of tea for the price of just over two old pennies.
Then, as now, catering had extremely narrow margins, and J Lyons took an early interest in computers to help automate its back office and improve its bottom line. Specifically, J Lyons was watching the work of Sir Maurice Wilkes at Cambridge University, where he was building EDSAC, the Electronic Delay Storage Automatic Calculator, that performed its first calculation in 1949. EDSAC was a pre-semiconductor dinosaur, using 3,000 vacuum valves and 12 racks, with mercury for memory, and that lumbered along at a then mind-blowing 650 operations per second.
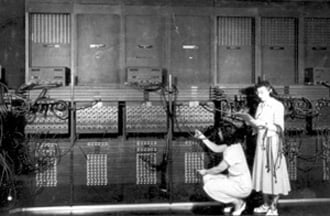
The ENIAC monster (photo: US Army)
Lyons copied EDSAC and came up with LEO in 1951, regarded as the first computer for business. LEO ran the first routine office jobs - payroll and inventory management - while Lyons also used LEO for product development, calculating different tea blends.
Lyons quickly realized the potential of office automation, built the LEO II and formed LEO Computers, which went on to build and install LEO IIs for the British arm of US motor giant Ford Motor Company, the British Oxygen Company, HM Customs & Excise, and the Inland Revenue. LEO computers were exported to Australia, South Africa, and the Czech Republic - at the height of the Cold War. By 1968 LEO was incorporated into ICL, one of Britain's few computer and services companies, now Fujitsu Services.
