This article is more than 1 year old
Creepy as hell: Facebook developers get to know you better
Home addresses and mobile numbers up for grabs
Facebook has added APIs for developers to access the home address and mobile numbers of users, so FarmVille can see where, as well as who, you are.
Permission to access such data must be given through the usual notification system, but with the vast majority of users simply agreeing with everything they're asked, the new facility is attracting privacy concerns beyond those incurred by sharing one's details with the developers of Bejeweled Blitz or similar.
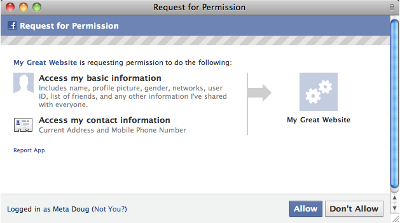
Users almost always click "Allow" when faced with such decisions, as demonstrated by Microsoft's Active X technology more than a decade ago and proven by the thriving malware ecosystem sustained by inattentive Facebook users today.
The alternative is pointed out by Sophos security, which suggests a more totalitarian approach: "Wouldn't it better if only app developers who had been approved by Facebook were allowed to gather this information?"
There are no Trojans on iOS or in the Mac App Store, so perhaps pre-approval is the way forward, restrictive as it is.
Sophos has said that the new APIs, applied on Friday, might be fodder for rogue application developers. Survey scams that form one of the mainstays of security threats on Facebook often attempt to hoodwink punters into supplying their mobile number and signing up to premium rate text messaging service of questionable utility.
The process of extracting mobile phone numbers of potential marks, which used to be a matter of social engineering trickery, might now be done much more easily. Users would still need to give permission for third-party Facebook applications to access this personal contact data but this has become a matter of fooling someone into clicking a dialogue box rather than the trickier process of hoodwinking them into typing in their mobile phone number.
Facebook recently beefed up its account recovery options to include messages sent to a designated mobile phone number as part of its account recovery procedure. This, and other factors, mean that the mobile phone number of many users will be held by the dominant social network.
Mobile phone numbers might even be held by the social network without users submitting them, in cases where their friends have recorded relevant phone numbers in their address book and make use of Facebook's iPhone application. More details on this privacy exposure can be found in a Guardian article here.
Sophos is urging users to remove their addresses and phone numbers from Facebook, as a precaution. A guide on reviewing Facebook privacy settings, developed by Sophos, can be found here.
Facebook's privacy dashboard can be found here.
The new APIs, launched at the weekend, also provide notification for developers if a user "unlikes" something: so next time you take a thumbs-up off a page, expect a phone call asking why, and perhaps a knock on the door from someone seeking a more detailed explanation. ®
