This article is more than 1 year old
Synology USB Station 2
Neat networker for external drives and printers
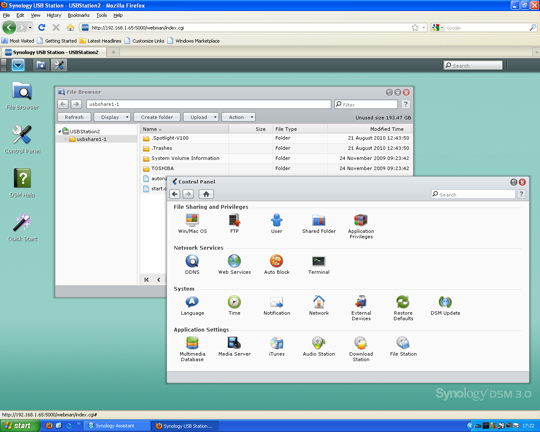
It handles account setup and configuration, so you can control access to parts of any drive you have connected to the device. Creating accounts and protecting areas of a drive may be necessary – even if you’re using the device in the home – as intelligent teenagers might otherwise indiscriminately fill your storage, but many people will still want to plug and go, and here DSM3 isn’t that convenient.
If you want to copy files from a local machine to a drive attached to the USB Station 2 you have to select ‘Upload overwrite’ or ‘Upload skip’ in the DSM3 file browser, and hunt for the local files in a separate dialogue – hardly intuitive. There’s also a filesize limit imposed by Java – 2GB for older versions and 4GB if you have the latest incarnation.
Better to map the drive attached to the USB Station 2, so you can treat it as a network drive under Windows. You need to run the Synology software on each machine that needs to access a drive or printer and there’s no ‘mapping wizard’ or auto-setup, which would make it friendlier for inexpert customers.
The device can act as a print server, which is a useful extra, and there’s a list of printers here that have been tested with the USB Station 2, but there are likely to be many more. Any well-behaved USB printer should work, though be aware this is only for network printing. The USB Station 2 doesn’t support network scanning from all-in-ones.
When I copied 4.7GB of data (a DVD’s worth) from a client drive to an external 320GB USB drive connected to the Synology device, it took 10m17s and copying it back took just over a minute less, at 9m14s.