This article is more than 1 year old
Quotes of the Year 2010
Our annual collection of the dippy, inane, and occasionally brilliant
“Avoid gripping it in the lower left corner in a way that covers both sides of the black strip in the metal band, or simply use one of many available cases”
"And make sure you keep your eyes focused on the shiny thing" - Steve Jobs' email to a customer explained how to cope with radio reception issues in the iPhone 4. Apple apparently ignored the advice of its engineers and carrier partner AT&T. It was forced to open its doors to to the press to show how arduous its multi-trillion dollar testing facilities are, made the phone's signal reception graphic look even more amazing, promised whinging users a free bumper... and the story completely disappeared.
“I predict that, in the future, someone will create a killer app that gauges the state of your mind, body, and spirit and automatically offers the exact steps you need to take to realign all three aspects of your being”
Ariana Huffington fails to realise that merely opening the box of a new iPhone 4 already does this. No apps needed.
“What we are seeing is that there are possibly minds in the universe that biology cannot get to, but technology might be able to get there. We are making minds that biology can't make.”
You may laugh at Kevin Kelly. You may snigger at his hot tub. You may mock his new book What Technology Wants, in which he calls humans domesticated cyborgs. But... actually, no - just carry on.
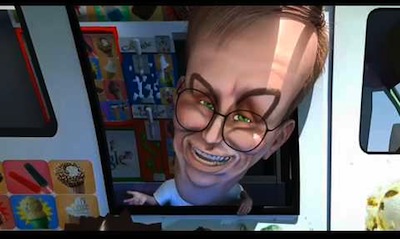
“Google policy is to get right up to the creepy line and not cross it”
The gift that couldn't stop giving - Eric Schmidt - was a firehose of memorable quotes. "We don't need you to type at all. We know where you are. We know where you've been. We can more or less know what you're thinking about," he suggested. “Street View. We drive exactly once. So, you can just move, right?” advised the Google boss before musing, "It's amazing to me that we let humans drive cars. It's a bug that cars were invented before computers." Your imperfections have been cruelly exposed, puny humans.