This article is more than 1 year old
Missile defence FAIL: US 'kill vehicle' space weapon flunks test
Fails to get in way of hurtling simulated nuke
The US Missile Defence Agency has suffered another embarrassing failure in a live test conducted last week over the Pacific.
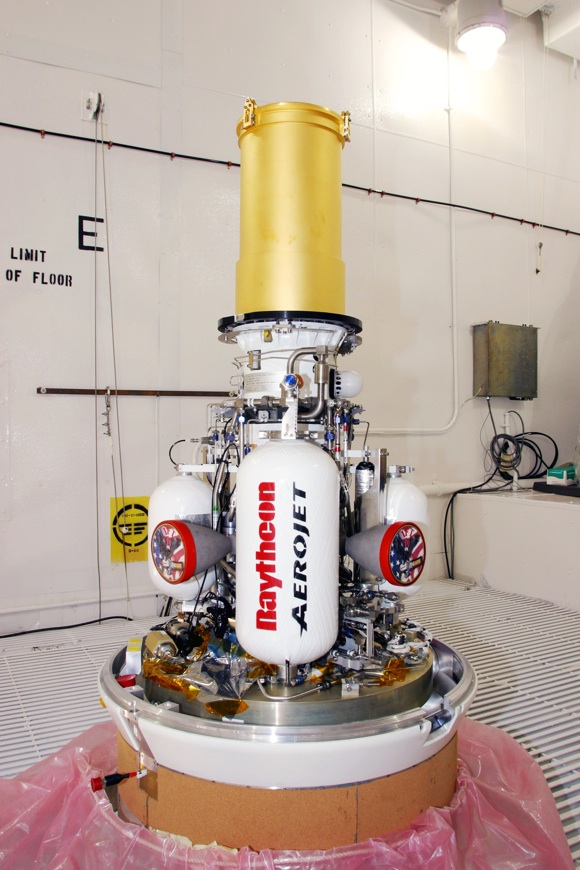
What a space-combat weapon actually looks like.
The trial saw a medium-range ballistic missile target lift off from Kwajalein Atoll in the Marshall islands, simulating an attack on the United States. The missile was was detected and tracked by the famous (and famously buggy) Sea Based X-band Radar, a large scanner mounted on a mobile oil-rig: this part of the exercise went without problems.
A Ground Based Interceptor (GBI) triple-stage rocket was launched from Vandenberg Airforce Base in California, the US military's main space base. Apparently the triple-stage GBI itself worked properly, depositing an Exo-atmospheric Kill Vehicle (EKV, pictured) in the path of the oncoming missile warhead.
What should have happened then is that the EKV should have used its small manoeuvring thrusters to get itself directly in the warhead's way. The combined many-thousands-of-mph velocities imparted by the rocket stacks of the missile and the GBI would then do the rest.
However, a Missile Defence Agency statement says that the MDA "was unable to achieve a planned intercept of a ballistic missile target", despite the deployment of the EKV being carried out "successfully".
"Program officials will conduct an extensive investigation to determine the cause of the failure to intercept the target," adds the MDA.
The expensive GBIs are supposed to be the most capable tool in the MDA's armoury, and are the only ones rated to knock out enemy warheads during the highest middle section of their ballistic flight. Under President Bush, the USA planned to site some of them, plus an X-band tracking radar, in Eastern Europe.
But the GBIs have a spotty test record – the naval Standard SM-3, which is launched from a destroyer or cruiser at sea and can also deploy an EKV into space, is considered more reliable. The SM-3 successfully destroyed a crippled US spy satellite in low orbit above the Pacific in 2008, and since the Obama administration decided against the European GBI deployment there have been suggestions that a land-based version of the SM-3 could perform similar tasks. ®
