This article is more than 1 year old
Sony PlayStation Network vs MS Xbox Live
Major consoles' online offerings rated
Head-to-Head The online functionality of games consoles has come a long way. Unrecognisable from the 14.4Kb/s modem sideshow curios on the SNES and Megadrive, and a quantum leap over Sega's iconoclastic Dreamcast, the Xbox 360 and PlayStation 3's online services can alone inform purchasing decisions. So if you're contemplating buying either for Christmas - or if you're daring to swap allegiance - here's a handy guide to their respective offerings.

Xbox Live (XBL) and the Playstation Network (PSN) are historically and philosophically chalk and cheese. A keystone of Microsoft's Xbox business model, Xbox Live is characterised by heavy standardisation, tight development control and unified services. The Playstation Network, on the other hand, is a far more decentralised, open system model.
Content
The past year has seen PSN close the gap on XBL, with the launches of VidZone, Mubi and Lovefilm joining the BBC iPlayer and PlayStation Store in offering free and paid-for streaming and downloadable content. PSN also has a built in web-browser and PlayStation Home - a Second Life-style virtual world. But despite an ever-growing library of games demos, minis, PSOne and PSP titles, Xbox Live still has the edge in gaming content.
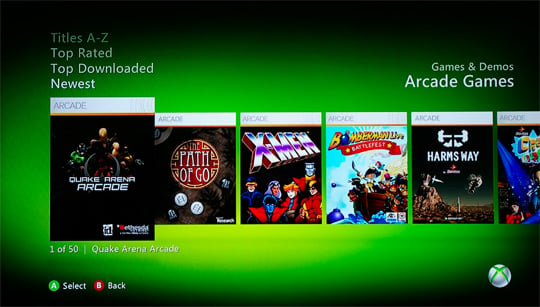
XBL has more games demos, add-ons, arcade-style games and independent games, as well as its Games on Demand service, where buyers can download full 360 and original Xbox games. XBL also has Sky Player, bringing streaming and on-demand services of popular Sky channels to current subscribers and monthly pay-as-you-watch punters.
Last.fm and Zune Pass offer free streaming and paid-for downloadable music. But with no sign of an additional US Netflix-style service, Xbox Live's movie offering is fast looking paltry in comparison to PSN's.
