This article is more than 1 year old
LaCie XtremKey all-terrain USB flash drive
Freeze it, cook it, dunk it, thump it
Cloud control
Talking of slow, included on the drive is software LaCie’s fledgling on-line file back-up service called Wuala. It requires registration and the product serial number is requested, so don’t throw away that packaging. The Mac version of Wuala is still in beta but seems stable. It creates a desktop drive with folders that sync to the on-line 4GB of storage you get for free or you can pay for more. Non-LaCie drive owners can use Wuala for free too, but lacking a product serial number, will only get 1GB.
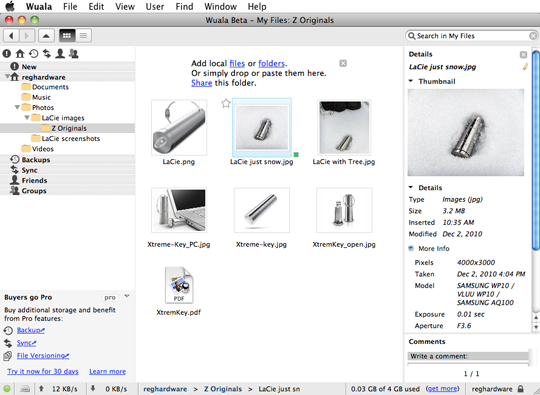
Wuala on-line storage will even show the EXIF data details of the stored image files
Click for a larger image
The default upload speed is 100kb/s – the on-line equivalent of watching paint dry – but a quick nose around the preferences settings revealed you can tweak the speeds to suit your ISP configuration. After changes I saw an improved average of about 320kb/s with peaks of around 400kb/s. Your mileage will undoubtedly vary.
Leaving drive out in the snow, dropping it from a balcony and immersing it in water did little to make an impression on its robust and well sealed casing. The only real issue was unscrewing the darn thing. It’s completely smooth and a knurled edge, like a coin, would be helpful to get the slippery thing open.
It was only after baking it for 15 minutes in the oven – as you would a typical pizza – and then cooling it off in water did a small stream of bubbles appear to suggest some ingress during this expansion and contraction. However, on opening it up, water was only present around the seal and a small part of the thread, the drive itself was still dry.

Environmentally tested
After baking, the XtremKey proved itself to function perfectly well, but it did have quite a whiff to it. It’s that acrid smell you get when a circuit board has met with an incendiary fate or you’ve held a soldering iron on it for too long. The whiff doesn’t go away in a hurry either, lingering with a hint of toxicity.
