This article is more than 1 year old
Meltdown ahoy!: Net king returns to save the interwebs
Cometh the hour. Cometh the Van. Again
Content re-distribution
CCN is his answer. CCN will cache content as it passes along the network and remember where it's been delivered. The next time somebody requested a hot story, CCN would remember where it was last downloaded and potentially direct you there, instead of to those central Google News, TMZ, Twitter or LA Times servers. That download could be on a local router or the smartphone of the guy sitting next to you on a plane.
The project also includes content authentication, according to PARC, so the content's publisher or the author can wrap it with their credentials to verify that the content is genuine.
When it comes to privacy, it's the data not the server endpoint that is encrypted. That gives the author the ability to say who's allowed to view their work. Data is signed cryptographically, so there's a notion of an identity provider, with the crypto key itself treated as just another content object. You, the content creator, manage and set identities for recipients of your data while CCN handles the encryption.
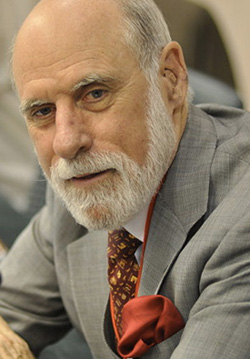
Vint Cerf: no idea what he'd unleashed with TCP/IP
That has a big pay-off for media companies concerned about digital rights management, but also for private individuals who don't like that all-or-nothing approach offered by Facebook and YouTube. Now you have more control over videos and posts fed to Zuckerberg's beast in the sky.
"Architecturally, you can make privacy the default, unlike now where privacy is expendable," Van Jacobson told us. "If you make the communications very simple and very robust, you can make access to the information highly controlled."
These are early days for CCN. The CCNx code is experimental and NDN is only just starting to think about turning Jacobson's idea into something that might actually work on a web scale. PARC has done proofs of concept at its Silicon Valley campus, and it's working with those unnamed commercial partners, who it reckons have bought into the CCN vision.
The real problem will be overcoming inertia — the inertia of those controlling the internet who feel they have too much time and money invested in the TCP/IP infrastructure to change, that they can simply throw a few billion dollars' worth of servers at the situation while recouping cost through tiered data plans for iPhone and iPad users.
There's also the potential inertia of Facebook and others, who quite like the commercial aspects of sharing your data with third parties. CCN doesn't just promise to change the internet's architecture. It also promises to alter who controls content online, and it will kill the carpetbagging business model of the web giants that make free money off user-generated content.
There's also the scale aspect. This is 2010, not 1988. There are hundreds of millions of nodes, not tens of thousands. It'll take more than a simple patch applied by willing sysadmins to fix this one. If we're talking about a major upgrade to the way the entire internet runs, we're talking about a fundamental shift in how the internet is built — right down the packet level.
According to Jacobson, CCN should at least have a low barrier to adoption from a technology standpoint. CCN has been architected to have the same universality as IP, which runs over Ethernet, Wi-Fi, and phone lines. CCN runs over these plus broadcast.
CCNx just hit its first mobile platform — Google's Android. PARC said Android — a Linux operating system that uses Java — was first on the list because it's "very compatible" with CCNx's code base — CCNx has a mix of portable C code and Java. The fact that PARC is engaged in research collaboration with handset maker Samsung also helped. Samsung, the world's second-largest mobile phone maker, is an Android convert that expects to sell a million of its Android-based Galaxy tablets in the coming year.
The future, again?
Van Jacobson, who recently showed us chat, email, and video apps all working with encryption over CCN, told The Reg: "You can deploy this over existing infrastructure. The web proxy targets CCN with a bog standard browser." The idea is not to rip out TCP/IP and start over.
It's a comment on Jacobson's drive and commitment that one of those who helped build TCP/IP should still be gnawing away at a system he helped refine nearly 30 years ago. Since those early days of beige flares and analog phones, Jacobson has devised algorithms to improve TCP/IP's performance over slow serial links; written network diagnostics tools traceroute, pathchar, and tcpdump; and worked on standards for Voice over IP and for multimedia.
With the funding now here to prove his idea on a web scale, will CCN be as big for the internet as TCP/IP was and as big as his subsequent work to help TCP/IP scale in 1986? "Ask me in six months... I'll give you an answer. They are working on that now," Jacobson says of the researchers now starting to work out how to deliver his vision.
Bear in mind that back in the mid 1970s, Jacobson with Cerf and Khan couldn't have imagined their work on TCP/IP would go on to revolutionize the planet, either. "It was a little thing that grew, and it grew slowly at first," Jacobson said of TCP/IP.
"Most people's perceptions of the internet was it happened in 1995, to others it happened around 1975. It stayed small until there was more general understanding and exposure to the ideas — and how simple and powerful the ideas were and what you could build with them. We hope we will follow in those footsteps, but only history will be the judge of that." ®
