This article is more than 1 year old
Top Ten Arcade Classics
Shinryuken! Feel my burning vigour!
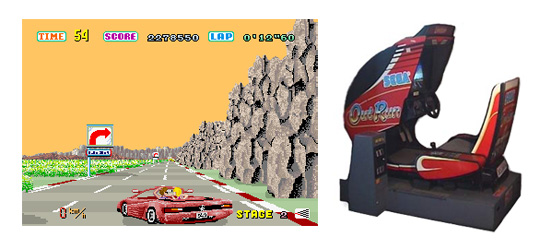
Sega Out Run

Driving a convertible racing along coastal roads, deserts and mountain ranges made this the pre-cursor to games like Ridge Racer. Unlike Pole Position, this game hinged on young male aspirations. Driving a blond chick around in a convertible has never been high on my list of things to do, but I do remember seeing boys flick 2p pieces up the slot to get credit on this game so it must have had something going for it. I guess being able to change the music using the steering wheel was pretty cool...
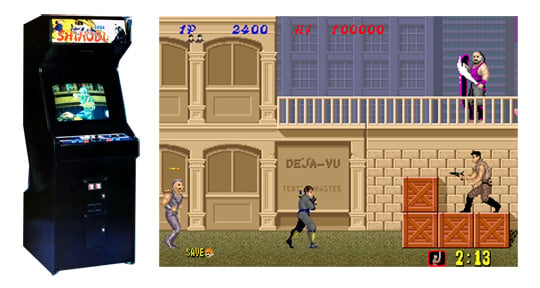
Sega Shinobi

With an unlimited supply of Ninja stars, ferocious punches and dangerous kung-fu kicks, Joe Mushashi remains one of the most formidable characters to appear in an arcade platformer. Mushashi's aim through five increasingly tricky levels was to reach the headquarters of evil kiddy-napping organisation Zeen, fronted by our hero's mentor, the Masked Ninja. With hostages to rescue and bosses to defeat along the way, Shinobi was an instant success, inspired several sequels and saw release on pretty much every home console available.
For all you shinoobies out there, a reworked version of the original can be found on Xbox Live. Ninja Magic!