66
This article is more than 1 year old
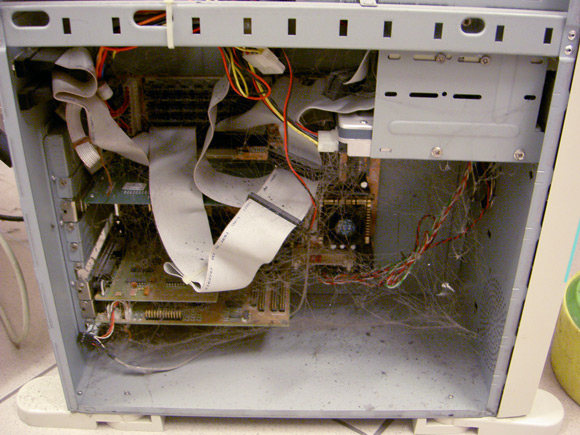
Dirty PCs: How much filth can you take?
The horror, the horror
Continuing with our US of A shockers, try this from Paul Ruby, Jr, who groans: "You know it is going to be a Monday, when this is your first computer to repair for the day."

You've got it: mice, and plenty of 'em.
Finally, Kai Flogaus felt he had to share this with us:

Nice. We'll leave it to you to decide just how that chilling round-up compares with previous submissions, and if you reckon you've got something even more repulsive, send me evidence here. ®
