This article is more than 1 year old
The forgotten, fat generation of Mac Portables
Long before the Air, there was Lord Lard Ass
Easy entrance
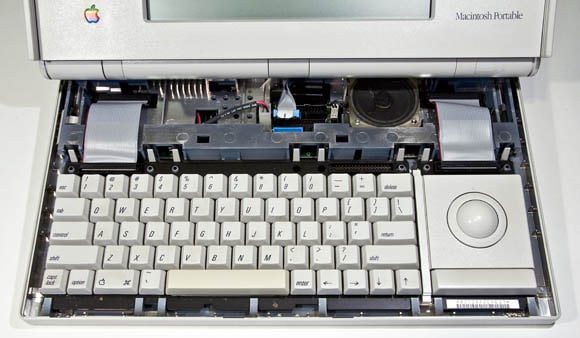
The Macintosh Portable was a snap — quite literally — to open for service and upgrading. Nary a screwdriver nor Torx wrench are needed to disassemble the entire machine, except for a small jeweler's screwdriver needed for some poking and prying. All is held in place by plastic or metal clips.

The Portable is easy to service — remember, Steve Jobs wasn't at Apple when it was designed (click to enlarge)
For easy entrace into the user-serviceable part of the Portable, you don't even need the aforementioned jeweler's screwdriver. Push two large buttons on the back of the case, and the rear cover lifts right off, revealing the hard drive, big-ass lead-acid battery, and expansion slots.
Removing the keyboard cover takes a bit of fiddling with that tiny jeweler's screwdriver, but once it's off, you'll discover a leftie-loving nicety: you can swap the placement of the 63-key keyboard and trackball.
What's more, if you'd prefer to use a mouse rather than the trackball — which, we hasten to add, works quite nicely — you can remove the trackball unit and replace it with an optional 18 key numeric keypad.
Which leads to a bit of nostalgic amusement. When the Portable was first introduced, the US edition of MacUser magazine welcomed it with a cover that showed a modestly dressed bathing beauty lounging in a swimming pool with her Portable on the arm of her floatation chair. She was also using a late-80s cellphone. So à la mode.
Unfortunately, the Macintosh Portable pictured on that cover had the keypad installed, and not the trackball — making it useless. A collector's item.
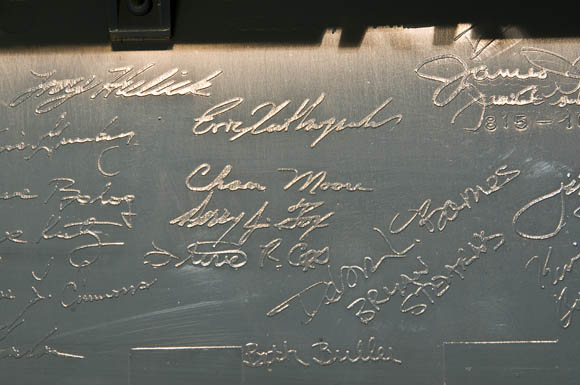
Upon removing the trackball and keyboard, you'll discover another artifact from a bygone age: the signatures of the Portable's design team in bas-relief on the case bottom.
This was the last time that such an element of humanism graced a Mac's case — the previous Macs so internally decorated were the original 128k Macintosh, the 512k upgrade of that original known informally as Fat Mac, and the Mac Plus.
We haven't yet cracked open a MacBook Air yet, but when iFixit did, no such evidence of the design team was found. Personally, we miss this human touch.