This article is more than 1 year old
High-speed asteroid pile-up prompts X-File
Astronomers probe 'peculiar' object
The Hubble Space Telescope has captured the aftermath of just what happens when two asteroids collide at 11,000 mph (17,702 km/h), prompting an explosion "as powerful as the detonation of a small atomic bomb".
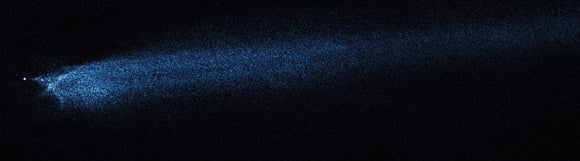
The result is a "peculiar" object - dubbed P/2010 A2 - which boasts a comet-like debris trail behind a mysterious X-shaped formation.
The asteroid belt pile-up happened in early 2009, according to NASA, but it wasn't until January this year that the Lincoln Near-Earth Research (LINEAR) Program Sky Survey spotted the tail.
Hubble's Wide Field Camera 3 observations indicate a surviving 400-foot-wide (122m-wide) object, which was hit by a smaller body, "perhaps 10 to 15 feet wide" (3 to 4m). The latter was vapourised in the blast, and its remains and material thrown off from the former were swept into a tail by solar radiation.
Astronomers are keen to find out just how much dust such high-speed encounters eject into interplanetary space, and while they reckon that "modest-sized asteroids smash into each other about once a year", they're difficult to spot.
But P/2010 A2 doesn't conform to the scientists' predictions. David Jewitt, of the University of California in Los Angeles, said: "We expected the debris field to expand dramatically, like shrapnel flying from a hand grenade. But what happened was quite the opposite. We found that the object is expanding very, very slowly."
The X shape, meanwhile, has the boffins stumped. NASA says: "The crisscrossed filaments at the head of the tail suggest that the colliding asteroids were not perfectly symmetrical. Material ejected from the impact, therefore, did not make a symmetrical pattern, a bit like the ragged splash made by throwing a rock into a lake. Larger particles in the X disperse very slowly and give this structure its longevity."
Jewitt and colleagues plan to turn Hubble's attention back to P/2010 A2 next year, in order to "see how far the dust has been swept back by the sun's radiation and how the mysterious X-shaped structure has evolved".
The P/2010 A2 findings are published in the 14 October edition of Nature. NASA has more here. ®
