Get these three right, and you're punching
Three things plague Nokia's product design and development today. One is bureaucratic inertia - and this has been so well discussed here at El Reg and elsewhere, I'll not elaborate here. The other is the fit and finish of the software and services contains such rough edges and loose ends, you wonder if the product managers are on permanent sick leave. Again, this has been observed so many times in so many products, repetition is unnecessary.
But curing those won't save the day. The third issue is a stultifying blandness and conservatism. In the 1990s Nokia had the courage to bring some radical designs to market. Here's one you'll know:
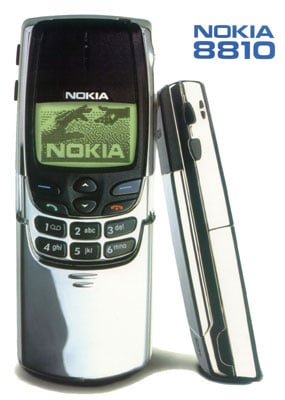
From 1998, the Nokia 8810: the absence of 7,8,9,0,# and * keys didn't stop it being a runaway success
The Nokia 3210, which sold 160 million, received just as much attention to detail, and was the result of different disciplines coming together under that elusive magic that's great design.
Today very little differentiates one E series (Nokia's best traditional phones) device from another, and the four new Symbian^3s are only differentiated from each other, rather than from the competition. The design doesn't do them justice. Rather like the old Soviet Politburo, the goal is internal conformity, rather than exciting and surprising the punter.
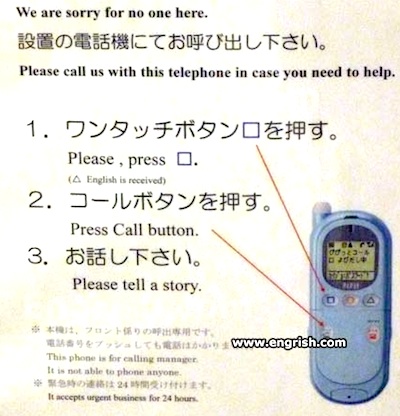
This is particularly noticeable in the software design, with Ovi a prime candidate. Was it really necessary to spend so long designing an icon set that didn't offend anybody, when the user can't tell whether the icon opens a folder or an application? Nokia really prides itself on its global cultural savvy, and when you consider that it conquered the world from the base of a tiny home market, you can understand why. But the savvy counts for nothing if the design looks like Esperanto sounds. Nokia aspires to a uniform "design language" - but sometimes, that language sounds like Engrish.
 .
.Now if I knew the answer, I wouldn't be sitting here. But recognising the problem should be a priority for the new CEO. HTC has shown what you can do with applied design. It's quite scary. ®
