This article is more than 1 year old
Yahoo! search! accordion! prods! you! to! squeeze! box!
Have you ever been experienced?
Yahoo! refined its search results yesterday, as the company continues to plod along underpinned by Microsoft’s Bing “decision engine” technology.
These days, the Carol Bartz-run web portal is focusing on prettifying its site, because it is in the process of transitioning its search results over to Microsoft’s prowess.
This means the company has found new and exciting ways to display searches that turn the marketing dial up to 11 for certain popstars and media darlings.
“We’re creating a search experience that, instead of merely presenting you with a simple list of results, lets you discover important, relevant information and get things done right after you search,” said Yahoo!
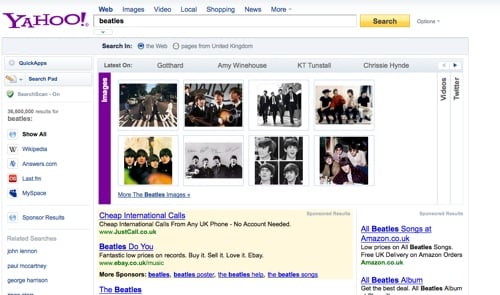
One of the new features added by the company is something dubbed the “Accordion tab”, which presents images, tweets, videos and the like in one unfolding webpage stack.
Here’s what we got when we typed ‘Beatles’ into Yahoo! via its US site:
And, in case you needed reminding what it is Yahoo! is actually here for in 2010, the company’s search and marketplaces veep Shashi Seth had this to say:
“We’re here to keep you entertained, productive, and informed so we hope you enjoy these new search experiences. It’s been less than two months since we integrated the Microsoft search platform for organic listings here at search.yahoo.com.
“We’ve been working hard to improve the quality and relevance for key topic areas on Yahoo! Search, including shopping and local results.” ®