This article is more than 1 year old
Sony Ericsson Zylo
A Walkman phone by any other name
Review The world + dog may be knocking out smartphones like there's no tomorrow but that's not to say the feature phones is dead and buried. The Zylo handset from Sony Ericsson would, once upon a time, have had a W code to show it sat in the Walkman range, but the days of simple delineation between music (Walkman) and camera (Cybershot) phones are long gone, to be replaced by a new era of slightly silly names – hence, the Zylo.
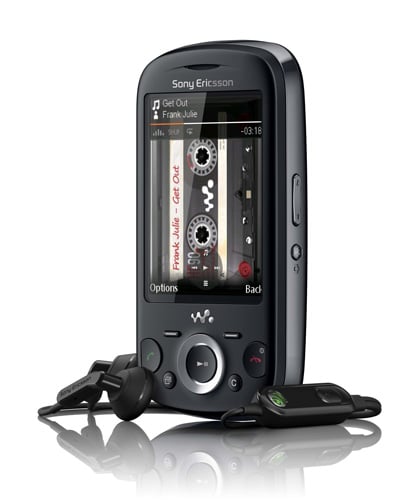
Sound credentials: Sony Ericsson's Zylo
The Zylo is all about music and social networking and consequently takes on a curious marketing duality where it's targeted both at kids who can't afford a smartphone and at those who kneel before the alter of sound quality.
The first thing that struck me about the Zylo was how well made it feels. It's light, solid and very well bolted together, despite being made entirely of plastic, and the slide action is firm and well weighted. Measuring up at 103 x 52 x 11.5mm when closed it's quite petite too, but still has room for a 2.6in 240 x 320 colour display.
The main controls are laid out in the traditional SE way with a central navigation pad that doubles as a play/pause control flanked by the call keys, two context dependent soft keys – which sit rather too far away from the screen corners for my liking – and small menu and clear buttons.
On the right side of the handset you will find a volume rocker and a Walkman button. The latter fires up the music player and acts as the camera shutter button once you have launched the camera from the main menu. Slide the handset open and you will find a keypad that is a pleasure to use. The keys are curvaceous, nicely sized and have a very clean action.

Just a 3Mp shooter on this handset
The user interface will be instantly familiar to anyone who has used a Sony Ericsson phone in the last few years. In fact it is very similar to that of the K850i I tested back in October 2007. The Media center interface looked fresh three years ago but things have moved on, not least on Sony's Walkman players, making it look just a little stale now.
