This article is more than 1 year old
Check Point defends ZoneAlarm scareware-style warning
'We didn't want to scare anybody'
Check Point has defended controversial marketing tactics that confronted ZoneAlarm users with what critics describe as a scareware-style dialogue box to convince them to upgrade to paid-for personal firewall software.
Users of the free version of the personal firewall were confronted by a warning that their PCs 'may be in danger' from a newly found variant of the infamous ZeuS banking Trojan. Users were encouraged to upgrade to the full-fat version of the product, which bundles anti-virus technology, via a linked page that dissed the ability of competitors, including AVG, Avira, Avast and Norton, to identify the threat.
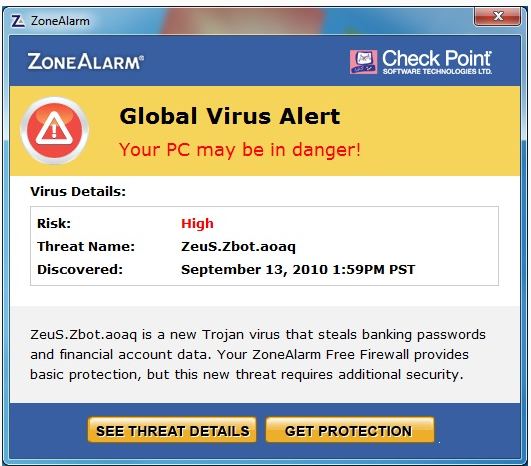
The warning appeared whether or not users were infected with any malware. No attempt was made to check whether users had any anti-virus software installed, a feature not bundled with free versions of the personal firewall. Users have complained on ZoneAlarm's forum that the warning was merely a pushy attempt to scare them into buying a paid-for version of the product, an accusation Check Point disputes.
In a statement, Check Point claimed it was simply pointing out the dangers of a prevalent security threat. It denied accusations that the warning message might panic users into believing they were infected with the Zeus variant.
The popup message in ZoneAlarm Free Firewall was intended as an alert to a virus our technology discovered. We wanted to proactively let our users know that ZoneAlarm Free Firewall and other AV products do not fully protect from this virus. It was never our intent to lead customers to believe they have a virus on their computer. This was purely an informative message about a legitimate and serious virus that also included information about the differences in protection of various products, and how to get protection against it.ZoneAlarm is committed to providing our customers with the best protection and considers it our job to proactively alert users whenever a potential risk is looming rather than wait for the damage to be done.
Check Point uses anti-virus technology licensed from Kaspersky Labs in its products, not software developed in-house. Kaspersky has a reputation for responding to malware threats quickly but its not always first. Check Point's unfavourable comparisons with other anti-virus technologies are based on a snapshot looking at detection for one malware variant at a particular time and could thus be safely ignored. The data was culled without permission from VirusTotal, a virus detection comparative service that has higher goals than to serve as an agent for marketing exercises of the type Check Point engaged in this week.
Security vendors are busy warning surfers about scareware-style warnings associated with fake anti-virus scanners. For a legitimate security firm like Check Point to adopt similar tactics is a great shame because it can only increase user confusion, especially if other suppliers respond in kind to the ZoneAlarm slur against the effectiveness of their products. ®
