And the winner is...
It will take me a long while to recover from the sheer pinkness of the Sony Vaio EB2 and my lasting impressions are of a laptop with few redeeming qualities and battery life that is, as I say, at the lower end of the scale.
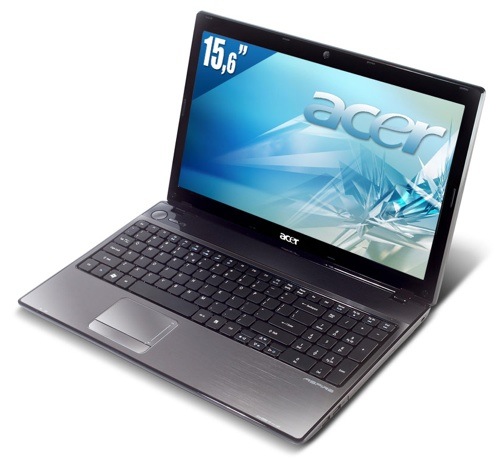
Acer's Aspire 5741: the Editor's Choice
I wanted to like the Toshiba as the low price seemed to offer some promise, but the low rent feel of the plastic chassis and the basic nature of the set of features removed the shine. Two USB ports and VGA output? Come on, Toshiba, you can do better than that.
The curious thing is that the winner, the Acer Aspire 5741, rose to glory thanks to a set of features that combine a decent Core i3 CPU with Intel graphics and decent battery life all served up with a low price. For all these reasons, it has to take home Reg Hardware's Editor's Choice award. ®
Netbooks Group Test
