This article is more than 1 year old
A quarter of Americans using mobile apps
But 35 per cent have them
The Pew Internet & American Live Project has been examining mobile apps, revealing the shocking news that rich people buy more applications, while the elderly poor buy fewer.
To be fair to Pew, which interviewed almost two thousand Americans for the study, the report does have some insight into how and when Americans download applications, though the vast majority of the data simply confirms what common sense would otherwise tell us.
Apparently, young, rich and well educated chaps download the most applications, which is hardly stunning news. The average number of applications downloaded (18) is skewed by a small number of people downloading huge numbers of apps (the mean is 10), which is equally unedifying.
More interesting is the fact that 11 per cent of those questioned had no idea if they had "apps" on their phones at all. Pew's definition includes applications pre-installed on the handset, but some users obviously don't include those, as the report points out - 34 per cent of mobile phone users admit to playing games on their handsets, but only 29 per cent of the same group said they used mobile "apps".
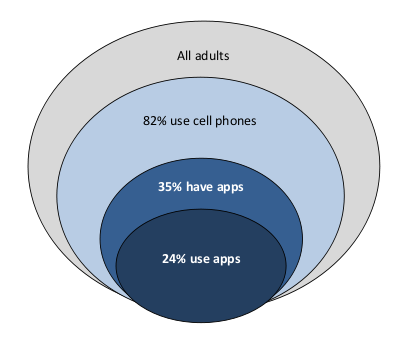
Figures for all Americans, based on asking two thousand of them
When it comes to downloading applications, 29 per cent of those with a mobile phone had done so, though less than half that number (13 per cent) had paid for the privilege. The latest research didn't look at how those users chose their applications, but the report does present findings from a larger, self-selected study which found that application stores are still the primary source of recommendations (49 per cent).
Next up were friends' recommendations (43 per cent), followed by web sites (18 per cent), with the network operator's home pages only just behind (17 per cent). Eight per cent of applications were found from within other applications, which makes sense given that the majority of embedded advertising seems to be for other applications these days.
A much more detailed breakdown by age, sex, ethnicity and so forth is available in the full report. It's worth a look if you're launching a mobile application, or just like having your preconceptions confirmed. ®
