This article is more than 1 year old
Pandora tops 1000 boxes
Open-spec hardware goes professional
English-built, open source games console Pandora has shipped its thousandth unit - not bad considering every one is hand made by geeks in Newcastle.
The Pandora isn't just a games console: running a tweaked Ångström Linux it can manage Open Office and Firefox too, all using open source hardware and software in a box the size of a Nintendo DS. Even the fact that it costs twice as much as a DS hasn't stopped 1000 people buying one.
It costs a shade under £240, though the company is sold out right now. The Geordie geeks are busy putting another another 3000 together in time for the busy Christmas period.
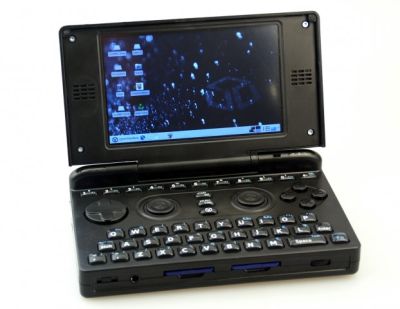
Those who find a Pandora under the tree will be able to play open source games including Quake 3 and Wolfenstein, as well as more than fifty developed specially for the platform. But equally entertaining are the 35 emulators allowing the device to run games and applications stretching from the PET to the N64, including MAME of course, as well as the inevtible video and audio codecs.
The Pandora isn't the only open-source pocketable gadget. The more financially-challenged might like to take a look at the NanoNote, which comes in at £99 and is proportionally less functional - last we heard they'd shipped 500 of them, and were rather enjoying themselves.
But the Pandora is a real business rather than a hobby, as the company is keen to emphasise: "People building the Pandora are paid a real wage and live normal 9-5 lives. This is a very important step for us so we hope you will consider it when deciding to buy your next console, we hope you will tell your friends about it too."
Open source hardware, just like software, treads a fine line - become too popular and you'll attract the attention of patent holders who can often destroy such efforts. The Pandora has gone professional, which is impressive, but it doesn't want to attract too much attention too quickly. ®
