This article is more than 1 year old
Google Instant blacklists the Slutskys
'Streaming' search doesn't give a f**k
Google's "Instant" search engine includes a blacklist for words and phrases involving what the company considers "violence, hate, or pornography."
Unveiled on Wednesday in the US, Google Instant serves up search results in "real-time" as you type. If you type "w," for instance, it gives you results for "weather." If you type "new" and then a space, it gives you results for "New York Times."
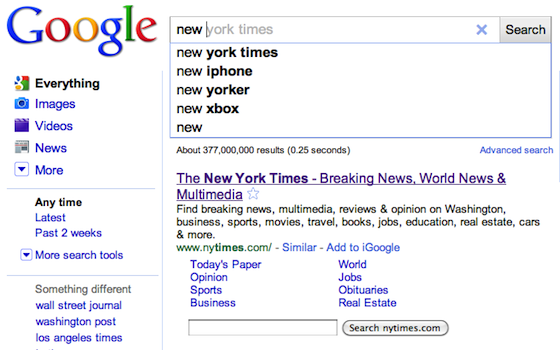
Google Instant
But if you type "fuck" or even "fuc," it gives you nothing:
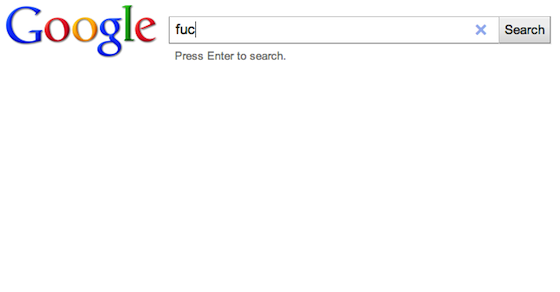
Google Un-Instant
However, if you type "fuck" and – in old school fashion – press the search button or hit enter, results arrive as usual.
Google revealed the blacklist on Wednesday morning at the press event introducing Google Instant, after a reporter named "Slutsky" pointed out that her name did not generate real-time results. "We care a lot about child safety and these kinds of issues, so we had to think a lot about auto-complete and how that works as you're getting the results," said Google product manager Johanna Wright.
"So we apply the same policies that we always have, whereby we filter for violence, hate, and pornography. As a result, if you're typing for something that may not be appropriate for certain people to see, you won't see results until you press enter."
Wright is alluding to the fact that Google also uses a similar black list with Google Suggest, the existing auto-complete feature that merely suggests searches as you type. The search giant doesn't want to suggest terms that young 'uns aren't actually typing.
The reporter also pointed out in blacklisting "Slutsky," Google isn't displaying real-time results for her great uncle, Russian mathematical economist Eugen Slutsky, known for his eponymous economic model the Slutsky Equation. And though Google wouldn't discuss this particular case during the Wednesday morning event, it would seem that the Slutskys are the victims of unnecessary collateral damage. Yes, they share four letters with a certain derogatory term, but once users type that "k," shouldn't Google auto-complete to something else?
The bug is not universal. When you type "fucc," you get results for "Fuccillo," a car dealership. ®
