This article is more than 1 year old
Oz pedestrians fall to 'Death by iPod'
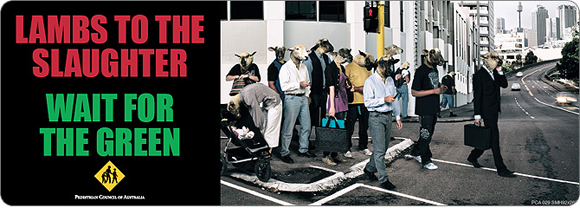
'Lambs to the slaughter'
Distracted Oz pedestrians are allegedly dropping like flies to "Death by iPod" - an untimely end provoked by walking out into traffic while in a "zombie trance".
While New South Wales road fatalities have dropped overall this year, "pedestrian deaths have climbed by 25 per cent to 53, compared to 44 for the same period last year", according to the Sydney Morning Herald.
The latest victim was a 46-year-old Sydney woman who walked in front of an ambulance on Saturday night while "reportedly wearing headphones".
"There is speculation she might not have heard the ambulance siren," the Herald notes.
The deliciously-named Harold Scruby, of the Pedestrian Council of Australia, told the paper: "'Death by iPod' is a relatively new phenomenon so it may be slow in showing up because it can sometimes be a year between the fatality and the coroner's finding.
"But we should be asking ourselves why are total road deaths declining while pedestrian fatalities continue to escalate? Maybe listening devices could be part of the explanation."
In response to the threat, the Pedestrian Council has put together a newspaper and billboard campaign to warn sheep that iPods and traffic don't mix:
While the powers that be have already attempted to address the problem, and "distracted pedestrians who cause accidents are liable for a $100 fine and face jail on more serious charges", Scruby demanded a more rigorous deterrent.
He said: "The government is quite happy to legislate that people can lose two demerit points for having music up too loud in their cars, but is apparently unconcerned that listening devices now appear to have become lethal pieces of entertainment.
"They should legislate appropriate penalties for people acting so carelessly towards their own welfare and that of others." ®
