This article is more than 1 year old
Her Maj gets Flickred up
Gawd bless yer Ma'am 2.0
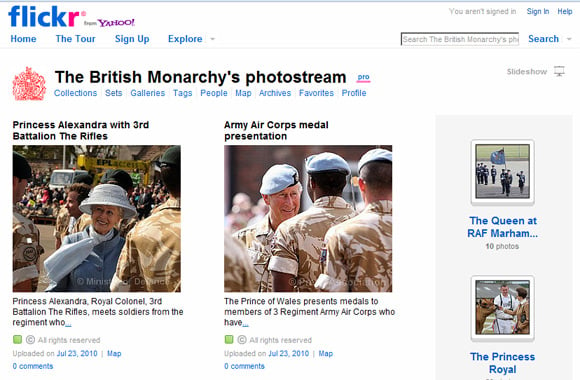
Buck House today launched its very own Flickr page, featuring lots of lovely snaps of the British Monarchy.
Currently on offer are 682 photos in 36 sets, with each member of the Royals given his or her own corner, so fans of Chaz of Wales can get straight down to it.
We're glad to see that the Queen of Hearts™, the sainted Lady Di, hasn't been given the cold shoulder, but most interesting is this set, showing Queen Vic and some early British photography.
Despite the best attempts of Associated Press, it's unclear whether Liz 2 is uploading the snaps herself from her iPhone while IMing Phil the Greek reminding her other half to fix the family's Twitter account.
An anonymous spokeslackey told the news agency: "We never comment on the queen's personal use of technology." ®