This article is more than 1 year old
Before the iPad, there was the Newton
MessagePad 120 – it didn't suck
A sexy beast — well, for the 1990s
The MessagePad 120, code-named "Gelato" during its development, was manufactured in Taiwan by Sharp for Apple — well, in those days, Apple Computer. Although the 120 appeared a mere 15-plus years ago, it's interesting to note how far miniaturization and fit-and-finish have improved in the ensuing years.
Check out, for example, the width of the seams and the lack of precision of the MessagePad 120's speaker grille — which, by the way, was a separate piece of plastic that slipped in between the top and bottom body shells, and which in a pre-Jobsian lack of hyper-precise stylishness had a not-quite-matching color.
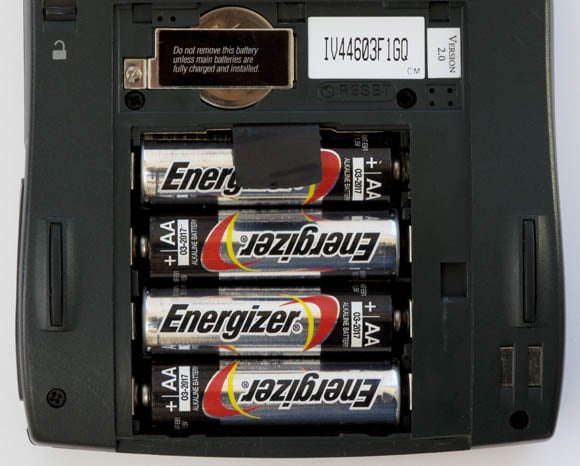
Another pre-Jobsian touch in the long-gone days of Newtonia was that all MessagePads, the 120 included, allowed users to replace their own batteries with store-bought cheapies. What a concept: user serviceablity, not user infantilization. A rechargeable NiCad pack was also available from Apple.
The MessagePad 120's infrared port was pre-IrDA — that standard wasn't implemented until the MessagePad 2000 and 2100, and the late, unlamented eMate 300. The 120 used the Sharp ASK (amplitude-shift keying) infrared protocol with Apple extensions — and if you want more info about those ancient IR days, check out the Newton Infrared FAQ.
In the paleolithic mid-1990s, even such straightforward hardware adjustments as contrast control were performed through dials, such as on the MessagePad 120. If you talk with service folks from those days, you'll learn that more than one MessagePad owner who thought their device had died was chagrined to discover that their contrast control had inadvertently been dialed back to zero.