This article is more than 1 year old
Cyberpower Ultra Scylla six-core AMD PC
Some kind of monster?
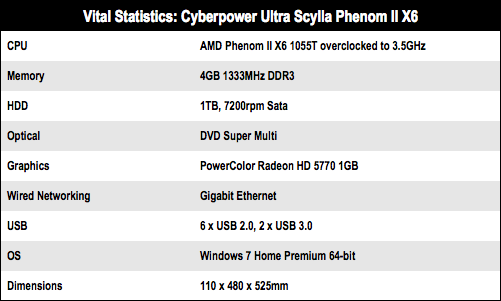
Moving on to the heart of the matter, the CPU is a 2.8GHz hexa-core AMD Phenom II X6 1055T that has been overclocked to 3.5GHz by Cyberpower. It’s interesting to compare the hexa-core technology used by AMD in Phenom II X6 with the Intel Core i7 980X. Intel had to shrink the Core i7 975X from 45nm to 32nm to squeeze in six cores. The quad-core has 1MB of L2 cache and 8MB of L3, which has increased to 1.5MB and 12MB for the hexa-core with the TDP holding steady at 130W.
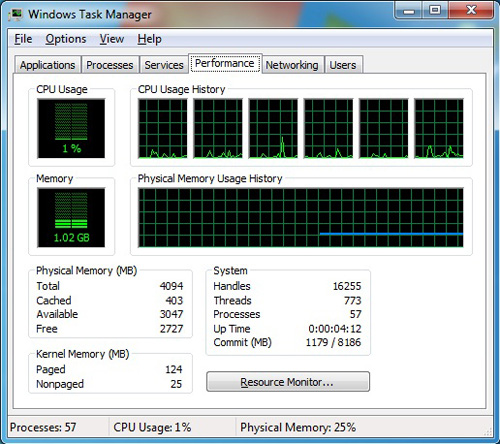
Windows Task Manager reveals the load on the somewhat untaxed six-core Phenom II
AMD, by contrast, stuck with its 45nm process and simply added two more cores to create Phenom II X6. The shared L3 cache stayed unchanged at 6MB and the L2 increased from 2MB to 3MB. This suggests that the Phenom II X4 core has a considerable amount of unused space. It’s also interesting to note that the TDP of Phenom II appears to be more dependent on clock speed, rather than the number of cores, as the 3.4GHz Phenom II X4 965 has a 140W TDP while the 2.8GHz and 3.2GHz Phenom II X6 models have a lower TDP of 125W.
Benchmark Tests
PCMark Vantage Results
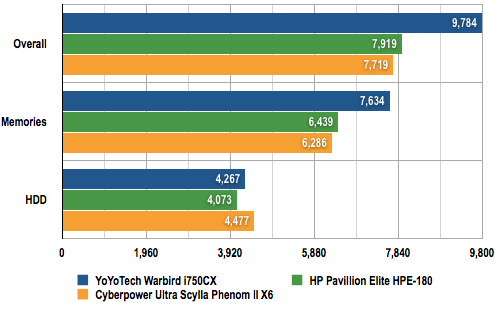
Longer bars are better
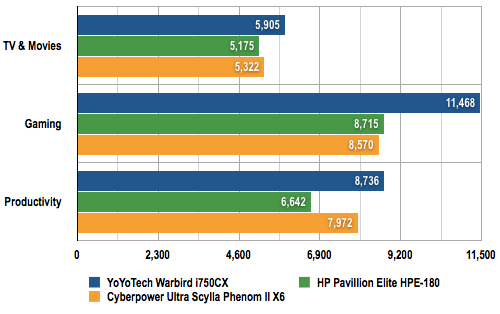
Longer bars are better
There’s a major difference between AMD and Intel in terms of pricing as the Phenom II X6 1055T sells for £170 with the faster Phenom II X6 1090T at £250 whereas the Intel Core i7 980X is priced at an epic £825. Cyberpower has overclocked the Phenom II X6 1055T by raising the CPU Voltage a tiny amount to 1.5V and also tickling up the chipset and RAM voltages slightly and then increasing the base clock speed to 251MHz to give a clock speed of 3.5GHz.