This article is more than 1 year old
Toshiba intros dual-screen, keyboard-less netbook
Mini laptop meets Nintendo DS
Hands On Toshiba thinks it has trumped the Apple iPad with a compact micro laptop that comes across as the mutant offspring of a netbook and a Nintendo DS.
The launch also sees the revival of Toshiba's long ignored palmtop PC brand: Libretto.

So, we have the Libretto W100, a clamshell mini machine sporting not one 7in, 1024 x 600 touchscreen but two, one where the keyboard usually goes.
The 840g gadget runs Windows 7 on a Pentium U5400, an ultra-low voltage dual-core part running at 1.2GHz. It has 2GB of 1066MHz DDR 3 memory and a 62GB SSD.
Toshiba's notion is that you can use the W100 as a netbook-style gadget - the lower touchscreen can present a range of virtual keyboards, including two different Qwerty layouts - one with big keys, one with small - numbers and a split-down-the-middle job for thumb typing.
The keyboard has haptic feedback, but on the sample unit I tried, it was weak and made little difference.
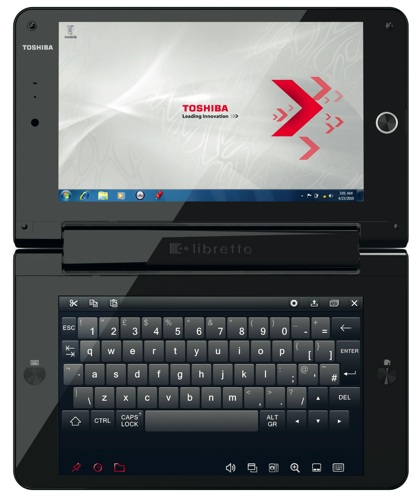
Get rid of the keyboard and open out the W100 to its fullest, flat extent and you have a sort of iPad wannabe spoiled only by the inch-thick hinge unit running across the middle. Rotate it through 90°, however, and you do have a nice book-style e-book reader.
The W100's dimensions a 202mm wide by 246mm, with the top and bottom sections both 123mm. The problem is the device's thickness - Toshiba cannily didn't say what this measurement is, but it's well over an inch.

This is a very chunk palmtop. That, and the two small screens in place of a single, big, tablet-sized one, gives the W100 as anachronistic feel, the sort of thing OQO or FlipStart might have come up with five years ago - and priced well beyond what mere mortals can afford, no doubt.
Perhaps it's no surprise, then, that Toshiba wouldn't say how much the W100 will cost when it goes on sale next month. ®
