This article is more than 1 year old
Apple's iOS 4 beams into unprepared world
Folders? Fine. Multitasking? Meh
How 'bout them folders?
The new Folders feature works as advertised. It's a simple matter to cram up to a dozen apps into a single icon-based container by holding and dragging them over first one app icon, then the folder that doing so has created. And although the folder is originally named with the category of the first app you drag over another app to form the folder, you can easily rename folders.

Left: folders can be renamed and can contain up to 12 apps
Right: A folder gets the category name of the first app dropped into it, but apps' categories don't need to match
To access any app in a folder, you merely tap on the folder and it opens up on your home screen. Launch an app by tapping it, or remove it from the folder by holding and dragging it onto the home screen. To delete a folder, just remove apps from it — when there's only one left, the folder disappears, and the app regains its original icon.
We'll dig deeper into the iOS 4 for a more-comprehensive review in the future. There's a lot more to explore: a unified mailbox, creating iPod playlists on the fly, iPhoto-based Faces and Places functions, built-in spell-checking, claimed improvements in photos and videos, and more.
And, of course, the iAds mobile-advertising platform, which is scheduled to go live on July 1.
But for now we'll leave you with one puzzling annoyance: although you now have the capability to choose wallpaper for both your lock screen and your home screen, we discovered that photos that looked just fine and dandy in iPhone OS 3.x now look like fuzzy crap in iOS 4.
We'll try reloading them from iPhoto when we get home, where we store all of our digital memories, and include our results in a future update. ®
Bootnote
One of the reasons that our installation process took so long was that the first 15 minutes or so were wasted on a failed download attempt. As the download continued — as this series of successive progress bars shows — the estimated remaining time steadily increased, then the download simply gave up the ghost.
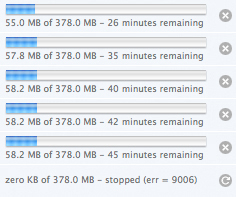
Apple's servers were hammered by fanbois furiously attempting to score their free copy of iOS 4.
