This article is more than 1 year old
Ubuntu v iTunes: the music playoff for Applephobes
Rhythmbox, Banshee, Daemon unleashed
Music Player Daemon
For those that think iTunes is bloatware and have always preferred WinAmp or foobar2000 on Windows, meet the Music Player Daemon.
Music Player Daemon is what it sounds like: a bare-bones background application that plays music.
MPD, as it's often called, is popular with some Linux fans because it's a great example of doing one thing well – playing music.
But of course, you'll also want to control your music while it's playing. For that, you need another application, something like the venerable Sonata or the Gnome Music Player Client, which offer the basics without all the "bloat."
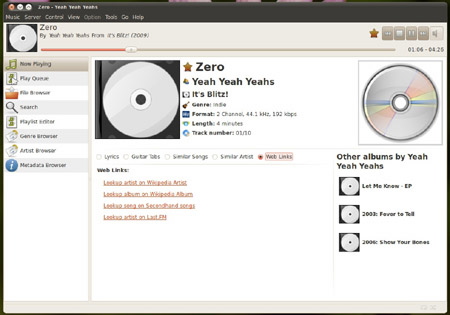
Gnome Music Player client in controls while you spin
If you're on an older system, or you just like to keep your apps lean and fast, Music Player Daemon is an easy way to do it – it's simple and no extra bells and whistles means you won't use half your RAM just to listen to a few songs.
Unfortunately, MPD and its accompanying control apps can be a bit awkward when it comes to managing a huge library of music.
Best of the rest
Still haven't heard of a player that's music to your ears? Well, there are literally dozens of Linux music players out there. Here are a few other options well worth investigating: Exaile, QuodLibet, Audacious, Songbird (technically no longer developed, but still available) and, if you're will to install the necessary KDE components, the ever-popular Amarok.
So which Linux music app is the best? Well, that's up to you. There is no such thing as the best piece of software, just the one that's most suited for your needs.
When it comes to music players, Linux doesn't just stack up well against the competition, it's actually well ahead of it, offering features you won't find on other platforms.
In this case, Ubuntu's default Rhythmbox offers everything those switching from Windows or OS X are likely to want, but as always there's an option to fit just about any need. ®
