This article is more than 1 year old
Pentax Optio W90 rugged camera
Whatever the weather
Certainly, it showed no short-term effects after being left in a pool of water in a freezer overnight. It complies with the IPX6 standard for dust ingress, which means it will still be running on dusty safaris across Africa long after you've wheezed your last.

Access to the innards is a twofold affair
The first unusual thing to note about the W90 is the lack of any kind of lens protection. "Lens protection" is a bit of a misnomer - the 28-140mm (35mm equivalent) lens assembly is safely housed behind a sheet of glass and, as is the fashion of reinforced cameras, doesn't poke out beyond the main housing in the name of safety.
However, with nothing to protect the front glass element at all, the front of our W90 quickly became smeared with fingerprint grease, fluff and other detritus that you can expect a ruggedised camera to pick up. Note: to real men, just remember to carry a hankie around with you.
Toughness aside, there isn't too much to get excited about in terms of the hardware. The top of the W90 is where the power and shutter release buttons live, and there's the usual gaggle of buttons on the back.
The battery and memory card, and the USB port and type D HDMI port, are hidden behind a pair of doors that require a double action to open. Pull down the switch with a fingernail, then slide the door open. It's fiddly, but that's preferable to a simpler single action, which could result in you accidentally opening the door while the camera's underwater.
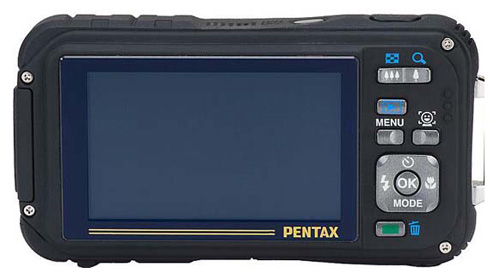
Sharp, bright screen – ideal for the great outdoors
The screen is excellent. The 2.7in diagonal feels roomy, even if its widescreen aspect ratio means framing up a 4:3 still wastes a fair amount of space. But it's exceedingly sharp, and bright enough that I had no problems using it in very bright sunlight.
