This article is more than 1 year old
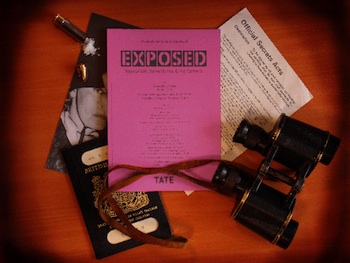
Exposed: Voyeurism and surveillance
Does it live up to the billing?
Surveillance is everywhere today, and thanks to Facebook and Google, we are all now voyeurs, monitoring each other electronically. Perfect timing, you would think, for the new exhibition at Tate Modern Exposed: Voyeurism, Surveillance and the Camera which sets out to explore our relationship with the camera and its use to capture the unaware, the unashamed and the downright unpleasant.
The show meanders through the dark side of the darkroom, from the earliest photography and, consequently, the earliest pornography, the camera’s role in social justice, celebrity stalking, scenes of violence and spying all feature. Here's a tour, with lots of links.
In 2001, Philip-Lorca diCorcia took shots of an unsuspecting public with a hidden camera. Entitled Heads the images wouldn’t seem out of place in advertisements. To diCorcia, the great unwashed were fair game and, when challenged in court by one of his unwilling models, a judge sided with the artist. Remember, this is art – resistance is futile.
Images by Walker Evans from the 1930s also depict the public on New York City’s underground trains. As with many of the photographs on display, acquiring these images was no doubt extremely challenging given the limitations of film, the available light and the covert shooting. Again, the work concentrates on the unposed demeanour of everyday people. Later, Evans’ work appears more akin to photojournalism, with his Sick flood refugee in the Red Cross temporary infirmary, a timeless image that, instead of Arkansas in 1937, could easily be a depiction of a recent third world tragedy.
Another photographer, Paul Strand took this a stage further, photographing impoverished immigrants using a camera with a false lens that suggested he was pointing it elsewhere. While not always covert, the prying images of the poor, taken either with social history in mind or for the schadenfreude effect, suggest another kind of vulnerability. The squalor revealed in the 1889 photograph Lodgers in Bayard Street Tenement, Five Cents a Spot by Jacob August Riis is another example.
Also on show are various concealed camera types: the heel of a shoe, the handle of a walking cane, a fob watch and one dating from 1886 that you’d hide behind a waistcoat with the lens appearing as a button. The classic Minox Model B spy camera appears along with a Leica IIIf sporting a Kodak 90° viewfinder.
The sight of a glass-cased redtop with its ‘Diana is dead’ spread seems somewhat incongruous and, like many aspects of this exhibition, the experience feels more museum than gallery.
