This article is more than 1 year old
3-million-km-long comet plunges into Sun
'Deepest penetration yet' filmed in STEREOvision
Boffins in California report that they have managed to track the course of an unusually resilient comet as it crashed deep into the Sun before finally being crisped.
"We believe this is the first time a comet has been tracked in 3-D space this low down in the solar corona," says Claire Raftery, a post-doctoral researcher at UC-Berkeley.
Raftery and her colleagues, fellow Berkeley postdocs Juan Carlos Martinez-Oliveros, Samuel Krucker and Pascal Saint-Hilaire, believe that the comet was one of the "Kreutz family", a swarm of comets - perhaps resulting from breakup of a single big one - knocked out of their previous path by Jupiter in 2004.
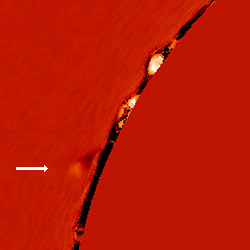
Hot comet plunge action.
The boffins managed to track one in particular, boasting a tail no less than three million km long, as it plunged down in a final death dive into the Sun. This was done using NASA's Solar TErrestrial RElations Observatory (STEREO) system. STEREO is a pair of observer spacecraft in orbit round the Sun, one ahead of Earth and one behind.
The STEREO track gave enough information to work out where the comet would crash into the Sun to within 1,000km or so. Raftery and her scientific chums then checked data from that area which had been scooped by the Corona instrument at the Mauna Loa Solar Observatory in Hawaii. Sure enough, these showed an object approaching the edge of the Sun at the right place and time.
According to the data, the boffins think that the comet actually survived a surprisingly long time, penetrating the solar corona and disappearing in the 100,000-degree heat of the chromosphere.
The four presented their research at a meeting of the American Astronomical Society in Miami last night. Comet-chasing isn't their usual work - seemingly it's more of a sideline.
“It was supposed to be an exercise, but it took over our lives,” says Raftery. ®
