This article is more than 1 year old
PARIS flashes some radio goodies
Beacon and GPS kit unveiled
The GPS set-up:
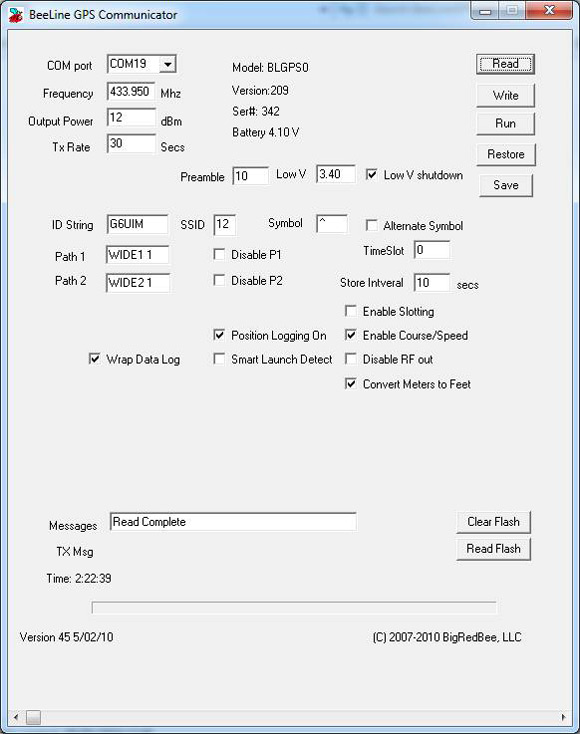
Frequency: This is the RF carrier frequency the packet will be sent out on. Possible values are 420-450 Mhz.
Output Power: Set between -10 dBm and 12 dBm.
Packet Interval: Number of seconds between packet transmissions.
Store Interval: Number of seconds between writes to on-board memory.
Preamble: Number of IDLE bits sent before start of packet data.
TimeSlot: Number of seconds to delay if slotting is enabled.
ID String: Your amateur radio callsign. Not more than 6 characters in length.
SSID: The SSID in the APRS packet. The default is 1, possible values are 1 thru 15.
Symbol: The symbol character in the APRS packet. The default is ‘-‘.
Enable APRS Packet format: When this option is checked, APRS position packet will be transmitted.
Position Logging On: Position and altitude data will be logged into o-board memory.
Enable Slotting: Turn Time Slotting ON. See below.
Enable Course/Speed: The course and speed are transmitted as part of the data packet.
Disable RF Out: Disables RF transmissions.
Wrap Data Log: When set, data is overwritten starting at the beginning after the end is reached.
Path: Each is 7 characters in length. AX-25 digipeating protocols.
Low V Shutdown Enable: Low voltage battery protection.
Read Data: Data memory is read from GPS and stored to disk (.kml file).
Smart Data logging:
Power On: When the GPS is powered on, it enters the base altitude state.
Base Altitude: GPS begins looking for a base altitude from the GPS engine. When it detects 32 consecutive valid GPS position reports, each with four or more satellites in view, the BASE ALTITUDE is recorded.
Launch Detect: The GPS begins looking for a launch condition. When three consecutive GPS positions report, each with four or more satellites in view, that is 100 meters above the Base Altitude, the state transitions to fill memory.
Fill Memory: The GPS records latitude, longitude and altitude data, wrapping when it reaches the end of memory, and continues writing up until the 32 samples before the sample where launch detect was stored. When memory is filled, the state transitions to full: While in this state the altitude is preceded with the ‘V’ character.
Full: No more samples are stored into memory. While in this state, the altitude is preceded with the ‘F’ character. Data packets are transmitted continually.
The normal progress through the state machine will be as follows:
* : Detecting base altitude.
^ : Waiting for launch.
V : Launch detected.
F : Memory full.
