This article is more than 1 year old
Labour manifesto changes a byte bit
But is that the only bit?
If you thought that what a party puts in its manifesto is a cast-iron guarantee of promises to the electorate, then think again – because the Labour Party appears to have no qualms about amending its online manifesto, post-publication, and hoping no one will notice.
The change is a technical one: a mildly embarrassing typo suggested a Labour commitment to give "virtually every household in the country a broadband service of at least 2 megabytes per second by 2012".
As a sharp-eyed reader pointed out, they must mean 2 megabits. A commitment to a 2 megabyte broadband speed would actually imply something like 16.8 megabits – which is well beyond the physical capability of the UK telecommunications system.
As it stood, this was no more than a minor embarrassment: yet further evidence that New Labour – like most politicians – have a poor grasp of IT technicalities. But take a look again today at their manifesto, same page, same para and the typo has been magically corrected. Labour are now committed to the more accurate pledge of 2 megabit speeds by 2012.
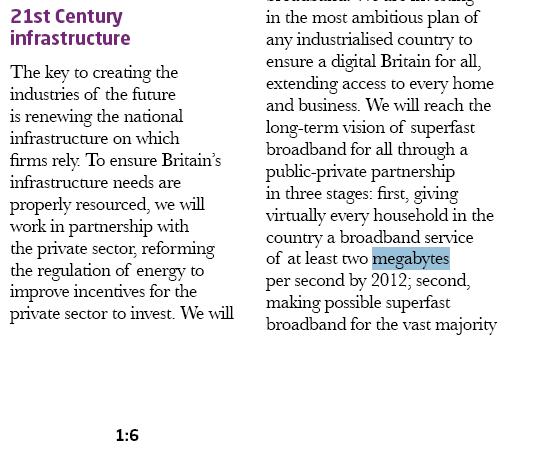
The Labour manifesto before, promising all the broadband you can eat...
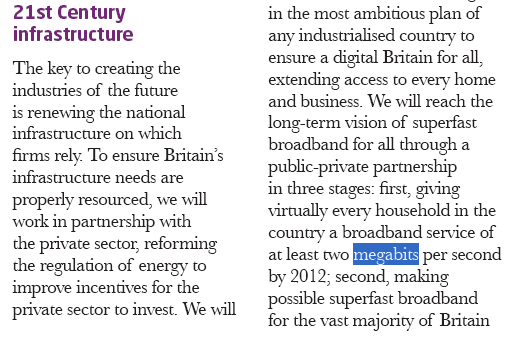
...and after, with a decidedly more modest offering.
The only problem with this correction is that – as far as we can see – there is no acknowledgment of any amendment having been put in place. This is widely recognised as an issue when it comes to online publishing: the ability to change what appears and therefore to rewrite the past.
Readers of a literary bent will get a whiff of Nineteen Eighty-Four, which featured this technique heavily, with the all-powerful Big Brother state constantly editing the past so that citizens were never able to depend on knowing their own history.
On the surface, this is small beer. But look again. Originally, the rogue speed appeared on page 1.6. Now it is on page 1.7. What else has been changed? Those with copies of the print manifesto may be able to tell us – but this ought not to be necessary.
Perhaps they have changed little - that's not the point. Labour have shown themselves prone to serious Big Brother tendencies – and once found out, the question remains: what else have they changed?
We have asked the Labour Party for comment, but so far we have not heard back from them. ®
