This article is more than 1 year old
Data Locker 1TB AES-encrypted external hard drive
Lock up your datas...
Assuming you've done so correctly, you can either connect the drive to the host computer, or enter the drive's set-up screens to change the default password, set a new encryption key, and/or turn off the annoying key-touch bleep.


Enter your password, and the drive mounts...
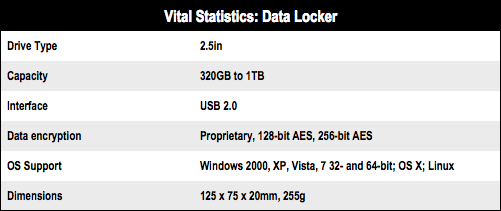
Origin, Data Locker's UK supplier, sent over the Enterprise Data Locker, which wraps all the data stored on it with 256-bit AES encryption, but the company also sells a Pro model with 128-bit encryption and a Personal version that uses a proprietary algorithm.

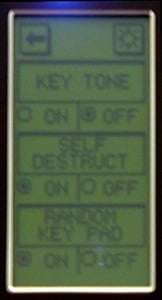
...or you can adjust the drive's settings
It also lacks the self-destruct mode of the Pro and Enterprise models - it deletes the encryption key after nine failed attempts to enter the password - and the clever keyboard randomiser, which changes the numeric layout every time its presented to you. The notion is that this will prevent the crafty herbert who has swiped your drive from working out the password by seeing where on the screen your greasy fingertips have been placed.
Data Locker also claims the drive is safe from malware in as much as it detects attempts to alter the file system and/or partitioning scheme and asks you if you do indeed want to delete all the data on the drive - a 1TB 2.5in Western Digital Blue in the review unit. It asks the same question if you intentionally reformat it.
You're free to format the drive to NTFS, FAT 32 or HFS+ and partition as you see fit.