This article is more than 1 year old
Space Station lightsabre-sparring hoverdroids to be upgraded
ISS mini-globes get tractor beams, crowdsauce greasing
Coming next - 'propellantless' tractor-beam formation flight
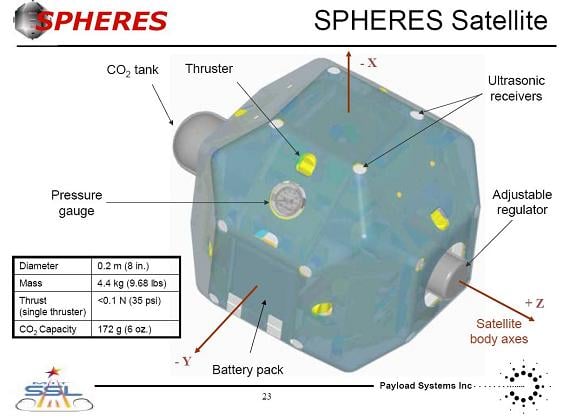
In any case, DARPA says that since arriving at the ISS in 2006 the SPHERES machines have been "primarily used as a formation flying algorithm testbed for graduate student research at the Massachusetts Institute of Technology (MIT)".
That's all very well, but the Pentagon propellerheads want to get on and make some use of the little machines' "expansion ports that allow new hardware to be configured on demand".
Needs tractor-beams, power-rays, that sort of thing.
Specifically, DARPA is ready to hand out cash for the following specific upgrades:
Firstly, a SPHERE capable of "vision based navigation", able to orient itself solely by observing another object - probably another SPHERE - and comparing the image with a 3D model of it. DARPA says:
The target object should be assumed to be moving and possibly tumbling, and its state will not be a priori known to the observer SPHERES (except through their own sensors). Once a 3D model of the object is constructed, the two observer SPHERES will perform relative navigation (as demonstrated through some test maneuver) solely by sensory reference to the target object and its 3D model.
Secondly, developers are invited to design a different upgrade enabling two SPHERES to largely cease use of their cold-gas jets and instead manoeuvre about each other using force fields generated by "steerable electromagnetic dipoles", "at a distance on the order of decimeters to meters".
