This article is more than 1 year old
Dell Inspiron One 19 Touch touchscreen all-in-one
Gives the finger to touch tech PC price premiums
Review Despite appearing on sale in larger numbers in recent months, touchscreen PCs still tend to be sold as luxury items with a price to match. So with the Inspiron One 19 Touch, which starts from under £500, Dell is deliberately giving the whole touchscreen PC market a boot up the backside.
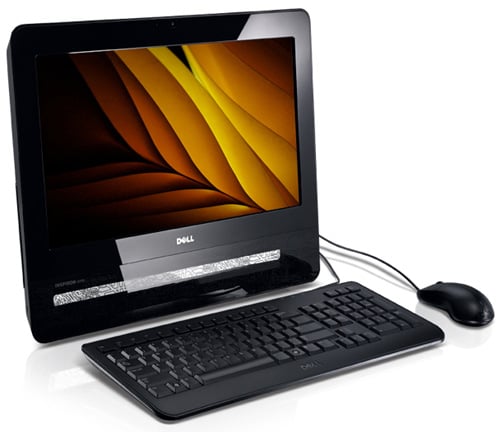
All fingers and thumbs: Dell's Inspiron One 19 Touch
It's certainly a bold move from Dell, whose previous desktop touchscreen offering, last year’s well-received Studio One 19, cost about twice that price. But does that just make the Inspiron One 19 Touch half as good?
The model on test here was the £549 base configuration featuring a 2.6GHz Intel Pentium Dual Core E5300 processor, 4GB of memory, a 500GB hard disk drive and one year of warranty, but Dell has just upped the CPU spec to the 2.7GHz E5400. The all-in-one display and system unit is encased in today’s obligatory glossy black plastic with a tough lean-back prop stand at the rear.
Despite the ‘19’ in the product name, the widescreen display measures 18.5in diagonally and has a native resolution of 1366 x 768 pixels. The bezel incorporates a webcam centred above the display and a pair of notably tinny sounding 2W speakers at either side.

Despite looking chunky from the side, it’s an impressively compact computer
The right-hand edge of the unit houses three USB ports, an eight-format media card slot, a Firewire port, and 3.5in stereo sockets for mic and headphones. There is also a pair of buttons for adjusting screen brightness, one of which can be used to call up the full menu of display controls. Further down this edge is a hard disk activity LED - essentially where no one will see it - and the power button.
